Some content can be unmoderated, though, so it’s worthwhile to be careful while using this platform. Facebook’s official dark web version helps users access the platform in countries where it’s blocked. During testing, I confirmed it provides the same functionality as the regular site while adding Tor’s privacy benefits.
Torzon Darknet Market
If the website you are trying to visit has Neutral mark it means we could not verify if this website is a legit or a scam one, since it has mixed reviews. If the website you are trying to visit has Recommended mark it means it has been verified and is safe to use. Fortunately, you can’t just stumble onto dark web websites by accident. No, it isn’t illegal to browse the dark web, and there’s nothing inherently wrong with visiting a Tor website.
- Surfshark supports unlimited simultaneous connections to protect as many devices as possible.
- For example, you can find information unavailable to the public and share data privately while protecting your online identity.
- Yes, governments can still monitor onion sites if they really want to.
- SecureDrop stands out as the leading platform for secure document sharing used by major news organizations.
- The New York Times operates one of the biggest news sites on the Tor network, letting users access its regular news coverage with increased privacy and security.
News And Journalism
Wasabi Wallet is a Bitcoin wallet that not only hides all your data in the Tor network but also allows you to “join” your transactions with others to increase your anonymity. This makes it incredibly difficult to find out who you are paying. It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder. NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites.
Ist Es Illegal, Webseiten Des Dark Webs Zu Besuchen?
Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. However, there are some significant variances in the background despite the similarities. For example, Whonix’s virtual workstation machine connects to the internal virtual LAN. It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved.
Other Privacy Tools And Services
For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. The system is designed to provide enhanced security and privacy features.

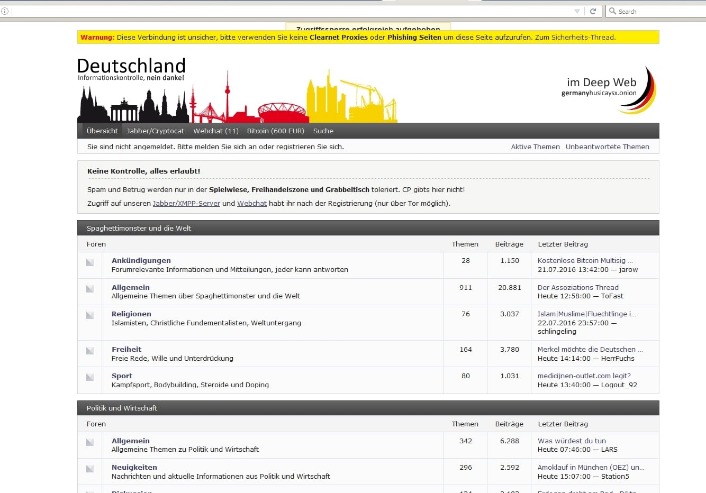
Internet = Gut – Darknet = Böse?

Other sites explicitly block search engines from identifying them. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. With the onion browser, you can access ordinary HTTPS websites on the web.
Hence, you never know when a popular .onion site is going to vanish, or even die. Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though). The best thing is to actually understand how to find the fresh, new links. You only need to upload your PGP key or let the platform create one.
A Quick Guide On How To Use A VPN With Tor
To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web. Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin. Think of Tor as a regular browser like Firefox, Google, or Safari. The only difference is that it passes your traffic through random nodes before reaching the destination. This means your activities cannot be traced or your browser history exposed.
Onion sites (aka Tor sites) are websites only accessible on the dark web; you can’t view them using a regular browser. Their URLs (aka dark web links) have .onion as the domain, instead of the common surface web domains like .com or .net. Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. Your online activity and communications remain private and secret on the dark web.
This makes Riseup a vital tool for people in oppressive environments or anyone concerned with online privacy. However, Ahmia doesn’t have a large developer supporting it, so it’s been the target of scams or cyberattacks in the past. So take this guide as you explore where to go on the Tor Browser without risking your online security. KeyBase combines encrypted messaging with secure file sharing and identity verification. Its dark web version provides the same functionality as the clear web option, while adding Tor’s anonymity layer. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security.
The platform stood out during my testing for its commitment to anonymity — all messages are fully encrypted and stored on a decentralized network. It’s particularly useful for sensitive communications that need to remain private. TorLinks maintains one of the most reliable directories of verified .onion sites.
- In 2025, 95% of markets prefer XMR over BTC’s public ledger, with transaction volume up 60% since 2023.
- The links shared in this guide were working during testing, but legitimate services occasionally move to new URLs to enhance security.
- This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks.
- Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts.
- Developed by the Freedom of the Press Foundation, the dark web site allows users to privately submit documents and sensitive materials without revealing their identity.
Top 10 Darknet Markets Of 2025
It also offers works of art, course material, and audiobooks for download. Impreza Hosting is a service that helps you host a site on the Tor network. It provides an .onion URL and an interface for you to manage your Tor site easily. It also boasts that no personal information is required to use the service, and payment can be made with cryptocurrency. Based in Switzerland, ProtonMail is an encrypted email service that is very popular with cryptocurrency enthusiasts.
Riseup’s secure email and chat help individuals communicate without fear of surveillance or data interception. Riseup provides email and chat services that keep no record of your online activity. Accessing ProPublica via the Tor Browser gives users an added layer of privacy and lets them bypass restrictive government censorship. This is especially important for individuals in regions where press freedom is restricted or where government surveillance poses risks to journalists and activists.