In 2019, rumors of a v4 onion service address emerged and many Tor onion service network administrators...
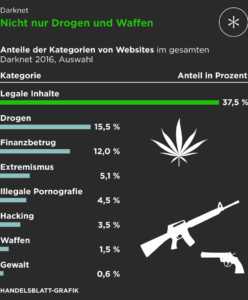
Another key aspect of these markets is their ability to offer a wide range of products, particularly...
It’s an ever-evolving ecosystem—constantly shifting, reinventing itself, and adapting. Versus Market allows users to leave detailed reviews,...
While they made no local arrests, the AFP had aided the global police effort by providing crucial...
But in 2013, law enforcement traced Bitcoin activity, monitored DPR’s forum posts, and exploited server vulnerabilities to...
Users must look for platforms employing robust encryption protocols, secure escrow services, and advanced anti-phishing measures. Additional...
Cybercriminals sellthis data to other malicious actors for identity theft, financial fraud andother illicit activities. The dark...
The combination of user-friendly interfaces, robust security measures, and diverse product offerings ensures a smooth and reliable...
Administrators and sellers on dark web marketplaces had a better 2023 than the previous year, pulling in...
According to OFAC, Nemesis Market facilitated the sale of nearly $30 million worth of drugs between 2021...