
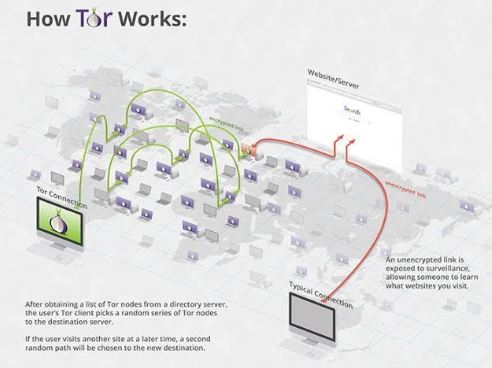
Although the social application is known for collecting data on its platform, it does not like sharing the information with others. If you know the right websites, you can easily access a tremendous amount of information, including research articles, news stories, and more. If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node. Though no one should bat an eye just because you’re attempting to access the dark web, keep in mind that in some countries, like the United States, even a simple foray can get you in trouble. Your ISP can’t see which websites you’re visiting on the dark web when you’re using Tor, but they might be able to predict or assume you are using Tor if they analyze your monitored internet traffic.
The forums also offer tutorials and guides on new hacking techniques as well as ways of improving existing skills. Therefore, such educational aspects attract a lot of aspiring cybercriminals who want to sharpen and take their abilities to the next level. Also, the forums offer community support, whereby they create some sort of community among the cybercriminals. They can easily and anonymously share knowledge, collaborate on projects, and even seek advice. It’s a type of support that facilitates the development of new techniques and skills.
How To Get On The Dark Web Safely FAQs
A VPN hides your internet activity, making it harder for your connection requests to be traced back to you. It’s a precaution to protect yourself before diving into the dark web. For recommendations on choosing a VPN, look for expert reviews and articles. Privacy and anonymity are the dark web’s hallmarks, thanks to a network of servers that hide users’ identities and locations. The deep web is just the part of the internet you can’t find with a search engine. It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications.
End-to-end Traffic Correlation
Lokinet is easier to set up than I2P, and it may run faster than Tor in some cases, especially when visiting regular websites through its secure network. However, its network is still small, and there aren’t many hidden services available yet. VPN-over-Tor breaks dark web compatibility, reintroduces trust in the VPN provider, and creates unnecessary complexity. With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with. Bear in mind too that laws about freedom of speech and censorship vary from country to country, which is part of the reason the dark web exists in the first place. Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn’t know exactly what you’re doing.

Other Ways To Access Dark Web Platforms
When you download and install the Tor browser on your device, you need to click the “connect” button on the landing page. You can use the Tor browser on Linux, macOS, Windows, Android, and iOS, and below are the steps for downloading and installing on each operating platform. However, how can you use it if you don’t know how to install the Tor browser on your device?
Which Is The Best Free VPN For Tor?
You can disable Javascript by clicking on “Preferences” in the macOS app or “Settings” in the Windows app. That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy. The compromised Tor exploit might trace back to you, but then again, your VPN will lead it somewhere else – which makes it impossible to be traced back to you.
Verified Social Channels And News Sites
These features are accessible from the Freenet interface under the “Community” and “Tools” sections. Hyphanet (formerly Freenet) is another anonymous network that allows you to share and retrieve information without censorship. It’s designed for secure, decentralized storage and is often used for file sharing and accessing information anonymously. Designed to be hidden from conventional search engines like Google or Bing, the dark web is a portion of the internet. Access to “.onion” domains and anonymous surfing made possible by specialised software like the Tor Browser allows entry only. Even though DuckDuckGo is the Tor browser’s default search engine, it doesn’t index dark web websites, which means you won’t be able to find .onion sites with it.
- Therefore, it’s considered not only legitimate but also highly valuable to those who are part of this notorious forum.
- It can help you bypass censorship or access location-restricted content.
- That way, they can easily combat criminal and illicit activities and also help to stop data breaches and several other potential malicious attacks.
- This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime.
- Despite some skepticism about its origins and privacy due to its military development, Tor remains the preferred choice for safe dark web navigation.
Are Sites On The Dark Web Illegal To Use And Visit?
On normal browsers, the IP address of your computer or router can be traced as you access websites. With Tor Browser, you’re assigned a unique browsing IP each time you open it. But as you surf during a session, entry nodes remember your browsing IP.
In March 2012 Russian hacker Yevgeniy Nikulin and three accomplices stole passwords for 117 million e-mail addresses from the social media company LinkedIn and then offered the data for sale on the dark web. In July 2016, passwords for roughly 200 million Yahoo! accounts appeared for sale. By using Tor and a reputable VPN, along with being careful and having the right tools, you can browse the dark web legally and safely. Responsible use protects your privacy while staying within the law, so it’s a safe place to browse for real privacy reasons. The dark web hosts a wide range of sites — from whistleblower tools and secure email platforms to underground forums, black markets, and dark web mirrors of legitimate news outlets.
Sending Group Texts On Pixel 6: The Definitive Guide
But if you are on the surface web, you should only use HTTPS sites. It’s important to note that you should always download Tor Browser from the official Tor Project website to ensure that you are getting the legitimate and safe version. Be cautious of downloading it from unofficial sources, as they may provide modified versions that could compromise your security. After completing these steps, Tor Browser will open, and you will be ready to start browsing the internet anonymously. Tor Browser is pre-configured with privacy settings optimized for secure browsing, so you can enjoy a higher level of anonymity right from the start. HTTPS uses a Secure Sockets Layer (SSL), which encrypts and authenticates information going between a browser and a website, and between servers.
Each address also contains cryptographic information that enables a dark web browser to connect to the site. That allows .onion sites to be accessible anonymously without services like DNS. Tor protects your identity inside its network, but it doesn’t hide everything.
Using a reliable antivirus to scan your device is worthwhile if you spot suspicious spikes in system resource usage. This isolates any potential malware and prevents cross-contamination with your personal data. Using Tails OS can further security, as all your data is reset every time you close the device. KeyBase combines encrypted messaging with secure file sharing and identity verification.
How Does The Tor Browser Work (& Keep You Anonymous Online)?
Practice safe, smart digital habits if you must use Tor to log into personal accounts. For instance, always use strong passwords that mix letters and symbols, making them hard to guess. Use different passwords for each account so that a single compromised account doesn’t affect others. Though secure against everyday threats, Tor is vulnerable to targeted attacks from state-level actors.



