Purchasing bitcoin in this manner is less private than using a P2P exchange such as Localcryptos. However, neither the payment processor nor the developers of Bitcoin.com Wallet will have any knowledge of what you do with the BTC once you send it to a darknet market. In other words, purchasing bitcoin via a service that requires you to complete know your customer (KYC) identification does not preclude you from spending those coins on the darknet or elsewhere.
With the Tor browser launched or a Tor private window opened in Brave, you’re now connected to the darknet and ready to browse. The seller will check their account and, when they see the funds, release the bitcoin that’s locked in the escrow wallet. Click ‘Wallet’ at the top of the page and you’ll see the BTC in your Localcryptos wallet. Click on the wallet and you’ll be taken to a transaction page where you can send your BTC to a different wallet – in this case one pertaining to the darknet market where you will be shopping. Avoid disclosing unnecessary personal information to strangers on the Dark Web. Be cautious when providing any personal details, even in seemingly innocent conversations or interactions.
- A virtual machine is a file that behaves like your computer while virtually borrowing a dedicated amount of CPU storage and memory from it.
- The dark web, a hidden portion of the internet inaccessible by conventional browsers and search engines, has increasingly become a marketplace for cybercriminals selling stolen data.
- When selecting a VPN service, it’s important to choose a reputable and reliable provider.
- Some regions ban the Tor network entirely, such as China, Russia, and Iran, so check your country’s laws before using it.
- However, when I broadened my query to “tech forums onion,” DeepSearch’s smaller index returned only five results, and I turned to Torch for more options.
Why Would An Organization Access The Dark Web?

Darknet markets (DNMs) supply all manner of goods, some legal, others less so, but all purchasable with cryptocurrency and delivered to your door. Indeed, many people’s first exposure to bitcoin is when they have the need to purchase something off the darknet. For shopping of last resort, you need money of last resort – bitcoin, or possibly monero. Speaking of exposed credentials, these frequently serve as the initial access point for significant cyberattacks, such as ransomware and account takeovers. When employee or customer login details surface on dark web marketplaces or hacker forums, it presents an immediate and exploitable vulnerability for your organization.
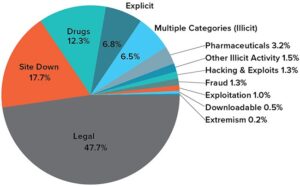
It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers. The deep web is just the part of the internet you can’t find with a search engine. It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications.
Official Security Advisories And Documentation
Naval Research Laboratory, enabled anonymous browsing via onion routing. Early .onion sites (e.g., hidden services for forums, blogs) emerged, but navigation was chaotic. Launched around 2007, The Hidden Wiki is a legendary entry point to the dark web, though not a traditional dark web search engine. It’s a community-maintained directory of .onion links, organized into categories like forums, marketplaces, privacy tools, and file-sharing services. No, while it hides your IP address and traffic, there are still vulnerabilities.
Step 4: Funding Your Darknet Account
Remember, the dark web isn’t just a den of iniquity; it’s a haven for privacy and free expression. Whether you’re a journalist, an activist, or simply curious, take the necessary precautions to remain secure. Before engaging in any dark web activities, I recommend researching official dark web sites ahead of time — use your regular browser to look online and see which sites are reputable.
Step 9: Maintaining Security And Privacy
However, integrating disparate protocols risks performance lags, necessitating lightweight designs like DeepSearch’s. I’ve used it to find reliable .onion services like ProtonMail quickly, and its Google-like UX feels familiar, easing the learning curve. But the opaque filtering process gives me pause—community reports aren’t as trustworthy as Ahmia’s audited system, and I’ve encountered risky links that slipped through.
On the order page, you’ll be prompted to enter the delivery address and select postage type. It’s up to you whether you wish to use your own name or an alternate name if the package is being delivered to your home address. Tick the box to confirm that you don’t reside in Australia and agree to the terms of service. If you already own bitcoin, or have obtained some using one of the methods described above, you can skip this section.
- This intelligence practice goes beyond traditional dark web forums, actively scanning the deep web, open web, and social media platforms.
- Adhering to these methods will help you safely locate legitimate resources while minimizing exposure to potentially dangerous or fraudulent sites on the Dark Web.
- Navigating through corporate investigations is a complex but essential task to ensure your company’s resilience against internal threats.
- When you search for something on Google or Bing, you’re using the clear web.
- It would be problematic if someone could open your private email chains through a simple Google search.
Can I Use Normal Search Engines On Tor Browser?
In this article, we discussed the background of the Dark Web and its association with both legal and illegal activities. Downloading and installing the Tor Browser is the first step towards accessing the Dark Web securely. The Tor Browser is specifically designed to provide anonymity and privacy while browsing the internet and accessing onion websites.
MITRE ATT&CK Framework Explained Your Guide To Cybersecurity Threat
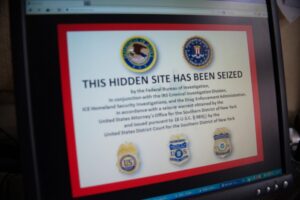
Visit a known .onion site (e.g., Ahmia’s .onion link) to ensure Tor is working. When your business detects a data leak on the dark web, an immediate and structured response is essential to mitigate damage, maintain stakeholder confidence, and meet compliance obligations. Follow these practical, actionable steps to respond effectively and protect your organization.
Is It Illegal To Enter The Dark Web?
Microsoft Word is one of the best word processors around, allowing you to craft powerful documents with an intuitive interface. If you know how to use Microsoft Word, you’re typically working with large files that span multiple pages. So, you’ll be happy to know there are several easy ways to delete a page in Word, including both blank pages and those you simply no longer need. The views and opinions expressed in this article are solely those of the authors and do not reflect the views of Bitcoin Insider. The information provided in this article does not constitute financial, investment, or trading advice. Every investment and trading move involves risk; this is especially true for cryptocurrencies given their volatility.
Open the VPN app and connect to a nearby server before launching the Tor Browser, and that’s it! You can download the VPN app from the provider’s official website or your device’s app store. Run the setup file and then simply follow the on-screen instructions. By leveraging these resources and staying connected with professional communities, you can keep abreast of evolving technologies, threats, and best practices.
This puts individuals at risk of being targeted by criminals or having their sensitive information sold to third parties. Exploring the Dark Web comes with inherent risks and potential dangers. It is vital to be aware of these risks and take necessary precautions to protect yourself and your personal information. If you come across suspicious links, you should avoid clicking on them. It’s important to verify the legitimacy of a website before interacting to protect your personal data and security.
Even when using security measures and your common sense, accessing deep web content still poses a risk. Antivirus will ensure that any viruses or malware downloaded from the dark web are removed. Tor routes your traffic through a chain of relays to obscure your IP address. This makes it harder for websites, ISPs, or surveillance tools to see who you are or what you’re doing. Many sites on the dark web are scams, and some host illegal content. Hosting a website on the dark web isn’t just for people with nefarious intentions.
Exercise caution when browsing the Dark Web, especially when accessing unfamiliar websites or interacting with unknown individuals. Be skeptical of claims that seem too good to be true and avoid websites that appear suspicious or untrustworthy. By following these steps, you can easily download and install the Tor Browser to begin exploring the Dark Web. Remember to keep your Tor Browser updated to ensure you have the latest security patches and features. The Tor Browser connects to the Tor network, which routes your internet traffic through a series of encrypted nodes. The Dark Web operates on a network known as Tor, short for The Onion Router.