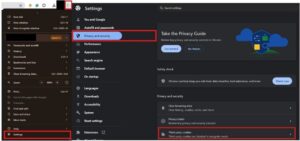
A VPN provides strong security for everyday browsing without the extra delays, middle checkpoint, and then finally the exit gate. The extra connection layers can act as a significant burden to your browsing experience if you’re doing something that is bandwidth intensive. This means that using the dark web may attract attention from your ISP or even law enforcement. To reinforce your privacy while on the dark web, consider adding on a VPN like Windscribe as an extra layer of protection.
Installing The Tor Browser
Avoiding these dangers means staying informed, sticking with trusted directories, and never trusting a .onion site just because it looks polished. On the dark web, appearance can be deceiving, and often, it’s designed that way on purpose. The Imperial Library is a hidden book repository filled with rare, controversial, and out-of-print materials that are hard to find elsewhere. It serves as an open-access digital archive with a focus on banned, historical, and suppressed works.
Should I Only Use A VPN To Access The Dark Web?
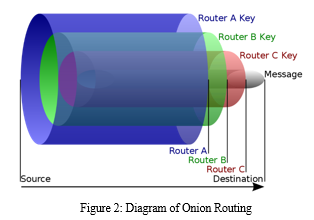
To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. In due course, the framework was remodeled and made public as a secure browser. These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes. No one is hiding here—they’re just guaranteeing that people in censored countries can read the news without being flagged.
Use Trusted Directories And Search Engines
It does not store logs and is protected from interference and malicious attacks. The platform is free and is run by volunteers in the US who prefer privacy and security. With ZeroBin, you can easily exchange encrypted messages within the dark web.

Email & Messaging Services: ProtonMail Onion, Sigaint, Ricochet Refresh
- However, many journalists, political protesters, and government agents also make use of the dark web when they need a secure way to communicate.
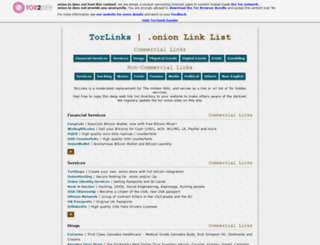
- I especially like how TorLinks categorizes links based on their type, letting you easily find what you need.
- The Internet is a vast and complex landscape, much larger than the familiar interface we use every day.
- For instance, if you choose a topic (e.g. food), G-Feud will give you a string such as “can I eat…?
- The BBC Tor Mirror is an international version of the BBC that focuses on world affairs, and it’s extremely useful for those who live under strict censorship laws.
- However, unlike commercial search engines, This is run by a confederation of volunteers.
Through the dark web, users in places of high censorship can also access information and news. TorLinks serves as a backup or secondary directory site to the popular Hidden Wiki. It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media). As always, use Tor Links with care, as it includes onion links to dubious or illegal activity. Haystak is a specialized dark web search engine with one of the largest indexes of .onion domains.
- The Dark Web refers to hidden websites that aren’t indexed by regular search engines like Google or Bing.
- Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously.
- He loves covering topics about VPNs, online privacy, and anonymity and shares his knowledge of online security with internet users through his words.
- In terms of functionality, I don’t think there are too many differences between regular IMAP, POP3, and SMT services and the stuff you can use to communicate on the dark web.
- Your activities on the dark web are not entirely shielded from tracking, and relying solely on anonymity can lead to a false sense of security.
- Facebook joined the dark web way back in 2014, and it remains a viable way to access the website in China and other countries that block it.
August’s Top VPN Discounts
Although content on the dark web is not as ‘indexed’ compared to the one on the clear web, you can still use search engines to find stuff. The deep web is just the part of the internet you can’t find with a search engine. It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications. Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet.
D Onion Websites: Between Anonymity And Risks
With the onion browser, you can access ordinary HTTPS websites on the web. This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity. Onion links have no regular domain names registered under the domain name registry. Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser. Hence, you never know when a popular .onion site is going to vanish, or even die. Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though).
Navigating .onion links and mirror sites safely requires diligence, awareness, and careful adherence to best practices. Remember, not all dark web activities are illicit—but it is your responsibility to avoid unethical and illegal content. Stay vigilant, respect others’ privacy, and consistently practice safe, responsible browsing. These onion websites are specifically designed to be accessed through the Tor network, a free and open-source software for enabling anonymous communication. The “onion” in their name refers to the multiple layers of encryption that protect user identity and activity, much like the layers of an actual onion.
This ensures greater security and privacy, making it much more difficult for snoopers to get in. Another standout feature is that the servers can’t see what you type, copy, paste, or send. To increase the security level, add password protection and determine the expiration time for messages. Onion.name is a dark web resource that helps make sense of the mess of letters and symbols that usually form the darknet sites. This is largely due to harmful elements in the dark web, and Ahmia contains certain questionable and largely illicit links. Therefore, use NordVPN to view search results and browse anonymously.

Onion sites use The Onion Router (Tor) software to encrypt their connections and enable anonymous communication. The dark web is the unregulated part of the deep web, which encompasses all parts of the web not indexed by search engines. While the deep web comprises about 90% of the total web, the dark web makes up just a tiny fraction of the deep web total. Deep web websites have to be hosted somewhere, and Impreza Hosting is one of those anonymous dark web hosting services. A host is basically a website’s house, or where it lives and takes up space.
Can I Use Normal Search Engines On Tor Browser?

Many of those sites are listed because their devs have submitted the site directly to the search engine for indexing. Unless you know where you’re going, there’s always some risk connected to clicking on dark web search engine links. Yes, governments can still monitor onion sites if they really want to. Local offices frequently monitor suspicious activities that involve their jurisdictions, so authorities might be closer to your anonymous communication than you know. Since most Tor websites are non-indexed and unregulated, the probability of scams is much greater on the dark web. Malicious actors can prey on unsuspecting users without leaving much of a digital footprint on Tor, so it’s often just a matter of time before you run into one.
Visit it to find out about Dark website closures, arrests, drug seizures, and other news topics related to the dark web and its use. The great thing about sharing via the Dark Web on SecureDrop is that users can do so without fear of persecution and without the possibility of being tracked down and punished. For this reason, it is always better to use a trustworthy VPN for Tor while accessing the Dark Web, as this will provide a robust additional layer of privacy.