However, it also supports legitimate uses like protecting free speech and accessing information in censored regions. You can buy credit card numbers, all manner of drugs, guns, counterfeit money, stolen subscription credentials, hacked Netflix accounts and software that helps you break into other people’s computers. Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account. The deep web is just the part of the internet you can’t find with a search engine. It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications. The dark web is neither entirely a haven for illicit activities nor a utopian space of limitless freedom.
What Kind Of Experience Do You Want To Share?
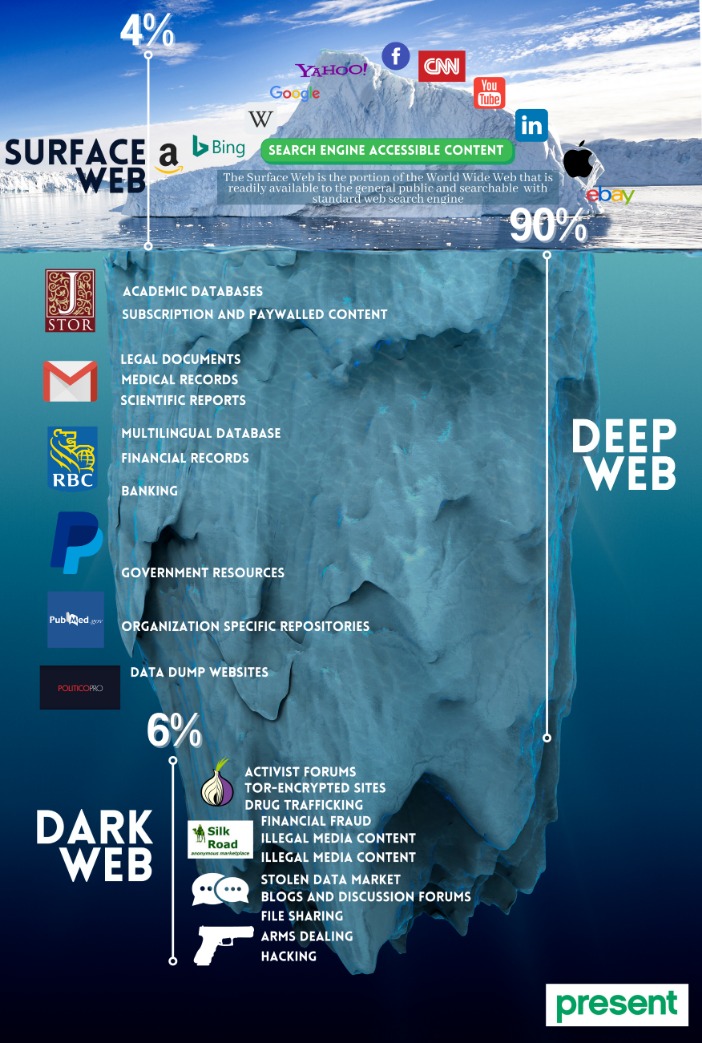
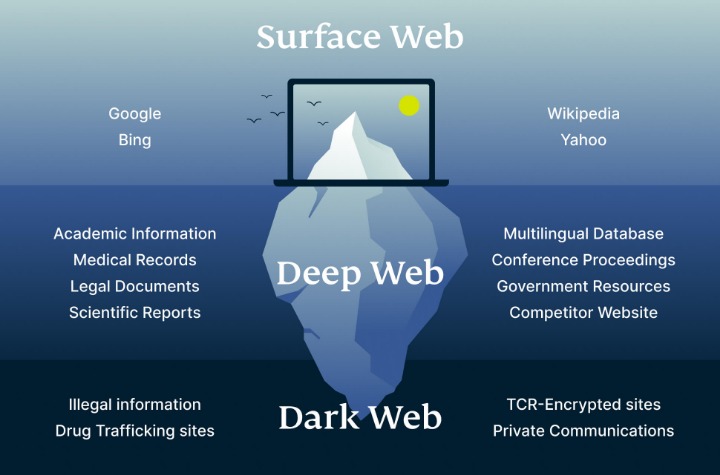
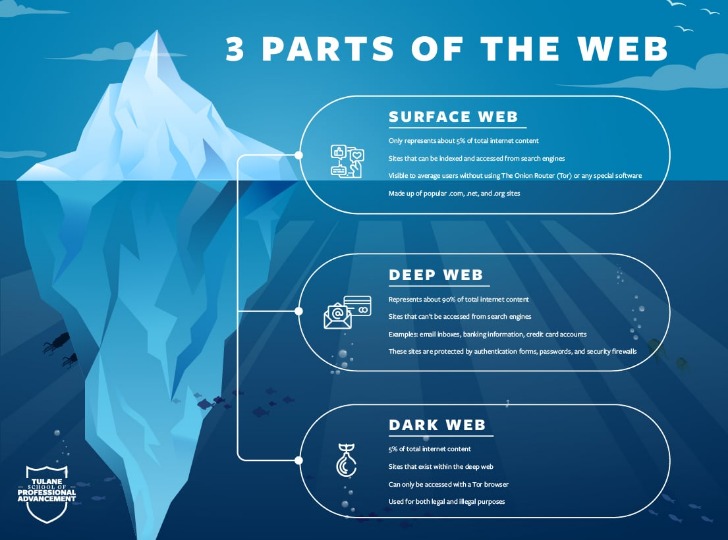
While the surface web is vast, it only accounts for a small percentage of the internet as a whole. Everything you can search for and interact with through regular browsers is part of the surface web, but much of the internet’s data is hidden below this easily accessible layer. However, while Tor is the most well known tool for the public to access the dark web, it was not the first. And there are now other networks and tools that provide access to the dark web, such as I2P, ZeroNet and Lokinet. Throughout the years, there have been multiple dark web social media services.
Understanding BlackCat Ransomware: Threat Overview And Protective Measures
These sites can be used by both hackers and individuals looking to exploit vulnerabilities. The dark web hosts a wide range of sites — from whistleblower tools and secure email platforms to underground forums, black markets, and dark web mirrors of legitimate news outlets. Proton Mail is an anonymous email service that operates an onion site. It is a useful tool for people who value their privacy and want to protect their communications with default end-to-end encryption, zero-access architecture, and minimal personal information requirements. Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor…. A virtual private network (VPN) is a good way to mask Tor activities.
The major advantage of using a live OS such as Tails is that, on shut down, the OS wipes itself from the thumb drive you’ve installed it. Fortunately, in Hidden Wiki, every website is followed by a brief description so that the user knows what to expect. You can also take a look at the blogs & essays section if you want to find some nifty coding resources. Well, now it’s time to fire up Tails and do a little bit of tinkering. Chill, because nobody will ever find a record of you ever fiddling around the darknet. Note that Tails’ installation package is the .img format, which means that you’ll need software capable of burning images on your thumb drive.
Drug Trafficking Sites
Especially for these people, the dark web is the perfect platform to communicate and publish information without having to worry about imprisonment or any other form of retribution. So, even though it does exist on the internet, Google doesn’t index any of these pages or content. We are committed to ensuring that our website is accessible to everyone. If you have any questions or suggestions regarding the accessibility of this site, please contact us. Would you be able to tell if a cybercriminal changed one character to send you to a malware-infested copycat site?
What Are EWallets And How Safe Are They?
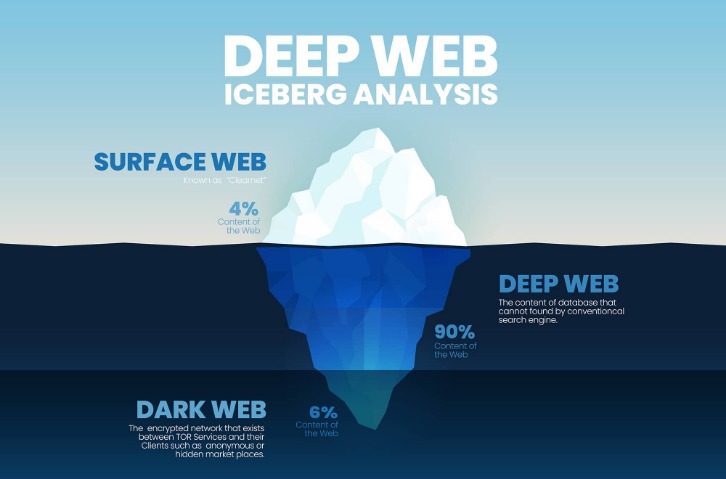
As the thesis project of Ian Clarke, a student at the University of Edinburgh in Scotland, the Freenet was built to help people anonymously communicate, exchange files, and interact online. Gannicus Oliver is an experienced tech journalist (he loves writing on emerging techs and digital privacy issues) and an online business consultant. In his free time, Gannicus enjoys uncovering thrilling adventures and traveling around the world. The child pornography site Playpen is one of the famous scenarios that resulted from the dark web. The site had only been up and running for about seven months, but surprisingly, it gained over 215,000 users. Deep down, the tip of the iceberg is where over 90% of the internet content is.
Hacking And Cybercrime Tools
Data breaches happen when a hacker steals user data from a company’s database. Generative AI is being used to fabricate synthetic identities, including deepfake voices, forged credentials, and AI-generated backstories. “Identity fraud is enhanced through synthetic persona generation and deepfakes, aiding criminals in bypassing know your customer (KYC) and biometric checks,” says Kroll’s Currie. “Threat actors are wanting to drive focus on their own brand names to gain more notoriety for themselves, such as the regular launching of new ransomware group brand names and leak sites,” says Carroll.
Protecting Against Malware And Exploits
You can check our guide on the best VPN services to find the right VPN solution to protect your privacy. The dark web has flourished thanks to bitcoin, the crypto-currency that enables two parties to conduct a trusted transaction without knowing each other’s identity. “Bitcoin has been a major factor in the growth of the dark web, and the dark web has been a big factor in the growth of bitcoin,” says Tiquet.
Recommended Security Measures
It routes traffic through several encrypted nodes, concealing user identity and location. These browsers grant access to.onion sites not indexed by normal search engines, allowing anonymous browsing. If you exercise due caution and use a combination of the Tor browser and common sense in which sites you access on the dark web, yes, the dark web is safe to use. You may be targeted by law enforcement, exploited by hackers, or threatened by criminals using the dark web for nefarious purposes. While law enforcement agencies around the world actively monitor these platforms and conduct coordinated takedowns, new marketplaces often re-emerge under different names or infrastructures.
Illegal Pornography
- For example we have a ‘staging’ version of this very website that is blocked from being indexed by search engines, so we can check stories before we set them live.
- It does support whistleblowers by offering them anonymity and secure communication in an oppressive regime.
- And most importantly, be patient as you’ve to sort through a lot of useless results.
- This type of government surveillance applies mostly to countries with environments that are hostile to free speech.
- But let’s be realistic, the best defence isn’t just playing detective after the fact.
Platforms such as whistleblower sites, political discussion forums, and alternative media outlets make the dark web a haven for those seeking to avoid censorship. Journalists, activists, and individuals in repressive regimes use it to share information without fear of surveillance or reprisal. Without the dark web, many of these folks would not have the ability to share and access critical information. Onion routing enables users to access .onion sites on the dark web, where each “layer” of encryption is decrypted only by specific nodes on the route, hiding the sender and receiver. Major organizations, including intelligence agencies, use Tor to safeguard sensitive communications.
You should never trust websites and forums on the dark web with your personal information. The dark web is a playground for hackers, cybercriminals, and people with nefarious objectives. We strongly advise you against visiting it, even if your intentions are good. These tactics trick users into revealing sensitive information or paying for non-existent products. Knowing about various types of ransomware and common hacks can help you better prepare to spot cybersecurity threats on the dark web.
- Slide up to the “safest” level, and as well as those settings, JavaScript is disabled on all sites.
- Though there are other ways to access onion websites, it is recommended that you always use Tor to access dark web websites.
- Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor….
- Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down.
- By using Tor, and especially in combination with a VPN, your internet signal is encrypted, making it invisible to your ISP.
- There are also dark web search engines, like Torch, that allow you to search for some types of dark web content.
You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web. For obvious reasons—I don’t want to get you or me into trouble, after all—I’m not going to get too specific when it comes to what you can find for sale on the dark web. A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous. Another private cryptocurrency you’ll find being used is Monero, which prides itself on being untraceable.
Some users, such as whistleblowers or journalists working on sensitive issues in oppressive authoritarian governments, need privacy to carry out their activities. Tor, short for The Onion Router, is a privacy-focused network that allows you to browse the Internet anonymously. It works by routing your encrypted traffic through multiple volunteer-operated servers, known as onion routers. Tor is by far the most widely used dark web network and is the biggest network in terms of content and activities. I2P, or the Invisible Internet Project, is an anonymous network layer to facilitate secure and private communication among its users. It works as a decentralized, peer-to-peer network that emphasizes censorship resistance and complete anonymity.