After that quarter, their number remains small, which is represented by the dashed line. In all panels, the dashed vertical line marks the time of operation Bayonet. Given the darknet’s infrastructure, which is hidden behind onion routing, the darknet attracts sites whose proprietors want to remain anonymous.
Nevada “Network Security Incident” Shuts Down State Offices And Services
Of course, not all the popular and widely-used dark web sites and things like marketplaces on the dark net are illegal. Some use them due to privacy concerns, such as journalists talking to informants or whistleblowers, while others may simply want to protect their confidential information from observation or tracking. Nevertheless, most people on the internet do not need to communicate or venture into the dark web. Ransomware has continued to see revenues in the hundreds of millions of dollars, but a number of large, multilateral law enforcement disruptions coupled with decreased victim appetite to pay ransoms have made a dent in the ecosystem. 2024 has nonetheless been a productive year, as attack volume was relatively sustained and some ransomware groups have still managed to eke out payments — albeit in lower amounts.
Full Network
While Bitcoin’s transparent ledger aids forensic investigations, Monero’s privacy features make tracing transactions difficult. In response, governments are enhancing blockchain surveillance and enforcing stricter regulations to combat crypto-enabled cybercrime. Cryptocurrency provides both financial innovation and potential for criminal use, posing problems to regulators and law enforcement. Blockchain transparency facilitates the tracing of transactions but is exploited by the veil of pseudonymity.

Darknet Marketplaces Around The World
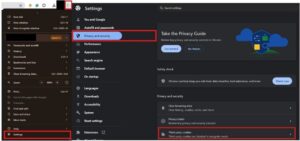
In terms of scope, this program covers various types of vulnerabilities, such as UI issues, server-side disclosure, sensitive data disclosure, authentication bypass, command execution, etc. There are four markets marked as half-filled circles under the “anti-phishing” column of Table 2. This means that these four markets alert users to check and compare whether the URL being accessed is the same one showing on the page, but without any form of verification. 2b shows another way to remind the user in the background of the CAPTCHA to check that the starting and ending characters of the URL address should match. Admittedly, those measures do not completely prevent phishing from occurring. Once an attacker completely clones a website and replaces the engine behind this mechanism (i.e. the method of verification), completely unsuspecting users can still be easily deceived.
Illicit And Risky Use-Cases
During this period deposits to darknet markets dropped significantly and no new leader emerged as vendors and buyers tended to avoid darknet markers while the dust settled. The median net income is positive for sellers while negative for buyers throughout the whole period of observation. In fact, when we compute the total net income for each seller, a considerable fraction (16%) has a negative net income because they spend in markets where they are not classified as sellers, or in the U2U network. Moreover, we find a change of trend between the seller and the buyer median net income time series which reflects the dominance of markets, as detailed in the next section. However, trading behaviour in DWM closely resembles what is observed on regulated online platforms despite their significant differences in operational and legal nature14. Nevertheless, due to their unregulated nature, DWMs exhibit behaviours not observed in regulated marketplaces.
Dark Web Markets: How They Work And Why They’re Dangerous
Therefore, the market usually only allows vendors with a certain reputation (or that pay a certain deposit to the market in advance) to enable this function. This mechanism is, in general, more beneficial to vendors than to buyers, because it ensures a faster turnover of funds and mitigates the impact of market exit scams. Information is gathered either while running a customised crawler or manually accessing the markets.

How Do Dark Web Markets Work?
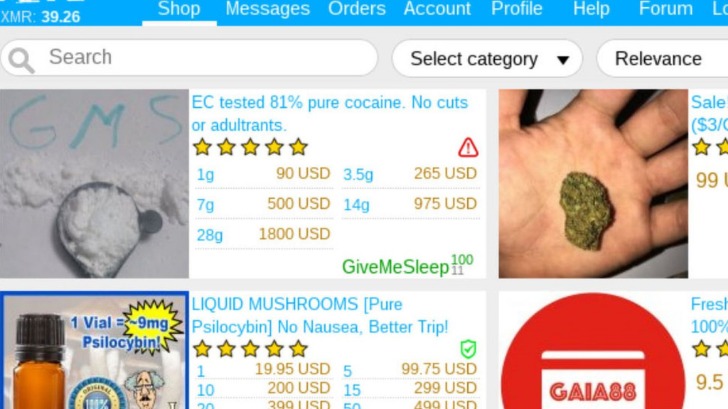
From items like drugs, fake ID cards, and hacked bank accounts to more complex offerings like human trafficking, these sites carry all the illegal activities you can think of. Although these marketplaces are continuously shut down by law enforcement agencies, they still work today. Interestingly, new sites get more hype, and it even becomes difficult to shut them down, as they have better security than the older ones.
Second, our approach does not explicitly classify buyers, which are entities that were not classified as sellers. There is a gray zone in which some sellers and buyers may not be easily distinguishable in transaction networks. For instance, there may be sellers that make a small amount of transactions, or spend more than receive, which we would classify as buyers. Nevertheless, it is important to stress that the results are robust under considerable variation of the parameters, indicating that the coherent picture emerging from our analysis does not depend on the details of the method. Future work may further extend the approach presented here, for example using machine learning methods to capture further behavioral regularities.
- Abacus Market launched in September 2021 as Alphabet Market, before rebranding in November 2021.
- Money laundering through NFTs thrives on anonymity and subjective pricing, making it difficult to track illicit transactions.
- However, we are not aware of any mechanism in the market to delete user accounts that have been inactive for a long time, although we believe this may exist but not be reported or well-known.
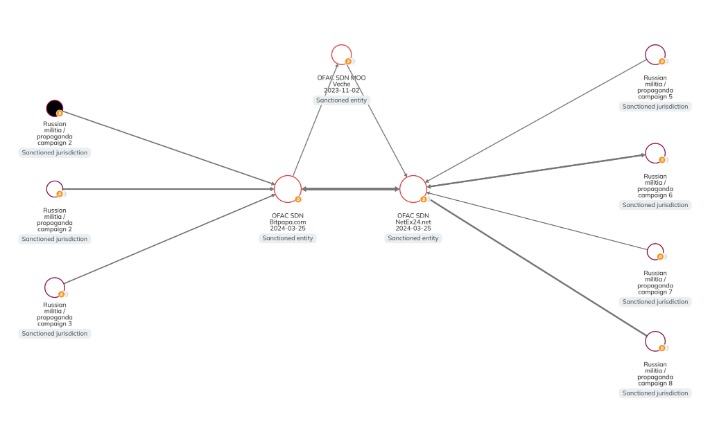
- Although some darknet operators, particularly of Western darknet marketplaces, have historically attempted rebrands or exit scams following law enforcement action, full-scale rebuilds appear to be becoming less common.
- Genesis Market and BidenCash, two top dark web marketplaces, were also shut down in 2023 and 2025, respectively.
- 7, we show the largest component of the S2S network one year before the operation Bayonet and one year after.
IREN Posts First Full-Year Profit On AI Cloud Growth, Mining Expansion; Shares Climb
Saheed earned his degree in Technology and Ethics from the University of Lagos in Nigeria. Since then, he has dedicated his career to writing extensively about crucial infosec, data privacy, and cybersecurity topics. When he’s not empowering PrivacySavvy’s readers to take control of their online security, Saheed enjoys distance running, playing chess, and exploring the latest open-source software advancements. If you’re using a browser like Tor and visiting .onion websites that aren’t accessible through regular search engines or browsers, you’re likely on the dark web. These sites often look basic or outdated, and their URLs are lengthy strings of random letters and numbers.

The Marketplace As An Arsenal
Retail vendors appear to be holding a greater portion of their proceeds on-chain than wholesale vendors, while wholesale vendors (those who distribute drugs in large quantities) are making greater use of DeFi. Besides Hydra operators, other DNM administrators faced criminal prosecution in 2024. The FBI tied Taiwanese national Rui-Siang Lin, Incognito’s operator, to the DNM’s website by tracing crypto transfers to an exchange account in Lin’s name. Lin was charged with a host of crimes, and by May, federal authorities in New York had arrested him. Financial innovation, including DeFi and CBDCs, must balance security and privacy. AML/KYC regulations for Virtual Asset Service Providers (VASPs) mitigate risks, but privacy-focused cryptocurrencies challenge enforcement.
Moreover, we observe a trend of increase in their median income relative to the value before operation Bayonet—an increase of almost six times by the end of the period of observation (see Supplementary Information S4). Further supporting this interpretation, we observe that the trading volume of the U2U network increases after Bayonet, while the trading volume of markets decreases (see Supplementary Information Section S4). In panels (b, c), we show the number of all sellers and buyers per quarter, respectively.
XRP Slides 4% Amid Bitcoin Selloff, But Cup-And-Handle Setup To $5 Intact
Then, you can set up 2FA (two-factor authentication) for that extra touch of security in case someone somehow figures out your password. If you ever have to connect to public Wi-Fi, make sure to use a VPN to keep your browsing safe and private. They’re tightening security and carefully screening anyone who wants to join. This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk.
We find that half of the DWM users trade through U2U pairs generating a total trading volume greater than DWMs themselves. We then show that hundreds of thousands of DWM users form stable trading pairs that are persistent over time. Users in such stable pairs turn out to be the ones with the largest trading volume on DWMs. Then, we show that new U2U pairs often form while both users are active on the same DWM, suggesting the marketplace may serve as a catalyst for new direct trading relationships. Finally, we reveal that stable U2U pairs tend to survive DWM closures and that they were not affected by COVID-19, indicating that their trading activity is resilient to external shocks.