And finally, we have political outcasts, refugees, and people who want to get in touch with the outside world, being from a totalitarian country that suppresses all means of communication and information. In terms of functionality, I don’t think there are too many differences between regular IMAP, POP3, and SMT services and the stuff you can use to communicate on the dark web. I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows. Because it’s easier to contain malware in a virtual environment, which can be fully controlled. Next step – your request will be transferred to Tor entry nod which in turn transfers to one or more Tor relays.
What Are Autoshop Marketplaces
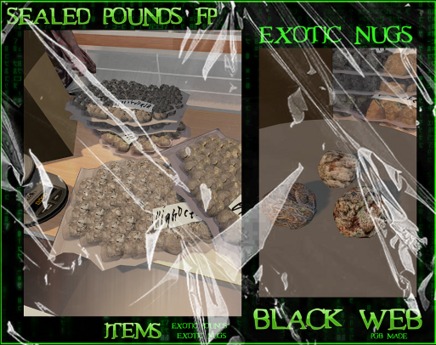
Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem. Based on our observations from analysis on dark web data using Lunar, we’ve identified the top 7 marketplaces on the dark web in 2025. We developed Lunar to monitor the deep and dark web, including dark web marketplace sites. You can conduct discussions about current events anonymously on Intel Exchange. There are several whistleblower sites, including a dark web version of Wikileaks.
Verified Social Channels And News Sites
In a world where data is a valuable asset and cyber threats evolve rapidly, understanding how dark web marketplaces operate is essential. While the anonymity they offer can embolden criminals, staying informed and taking preventive actions are key to remaining secure. Dark web marketplaces might seem impenetrable, but law enforcement agencies worldwide, particularly the FBI, have made strides in dismantling these networks. High-profile cases, such as the takedown of Silk Road and AlphaBay, have shown that these platforms can be infiltrated. Undercover operations and advanced digital forensics have led to the arrests of prominent dark web figures, sending a clear message to those who operate in these hidden corners of the internet.
Community Forums
The dark net is famous for being a hub of black market websites for buying and selling products and services. If you purchase something from such shops and make payment through conventional payment methods like your bank transfer, credit/debit card, or PayPal, you can be caught easily and face legal consequences. Using a dark web search engine is a great step towards enjoying a more secure experience while shopping on the platform.
- It offers outstanding privacy features and there is currently a discounted rate available through this link.
- A logless VPN, which doesn’t store any traffic logs nor session logs is highly preferable.
- Once a buyer makes a payment, it’s usually held in escrow until they receive what they bought.
- If you’re trying to hide from an oppressive government or want to be a whistle-blower for something illegal, take as many steps as you can to be safe.
- These insights provide context around cyber risks and help security teams adjust their defenses.
Microsoft Strengthens Security After China-Linked Attacks
Since the dark web can be accessed through the Tor browser, use a VPN with the Tor browser to ensure increased protection. A VPN hides the fact that you’re using Tor, which is blocked in some countries and always raises doubts because of its criminal reputation. Tor stands for “the onion routing project.” It was developed by the U.S.

How To Stay Safe On The Dark Web
Many people install a VPN as well, but then you’re putting your trust in an additional third party to not track your activities or report them to anyone else. Ethically, they must minimize harm, responsibly handle any stolen or sensitive data (often notifying victims or law enforcement), avoid entrapment, and maintain research integrity. An award-winning cybercrime threat intelligence firm, KELA’s mission is to provide 100% real, actionable intelligence on threats emerging from the cybercrime underground, to support the prevention of digital crimes. One of the biggest problems cybersecurity teams face isn’t a lack of tools — it’s too many alerts. And beware—while many explore out of curiosity or for research purposes, it’s important to remember that engaging with these platforms, even as an observer, can lead to serious legal and ethical consequences.

1 Anonymity Tools And Enabling Technologies
As you can imagine, bad actors around the world would be attracted to any method of keeping their illegal activities undercover, and began to appreciate the dark web as a place to more or less safely conduct their activities. In 2002 the dark web began to grow significantly when researchers backed by the U.S. The Tor Network provided a way to open safe communication channels for political dissidents, while also offering a channel for American intelligence operatives to communicate from around the globe.
- It was quite popular for selling a wide range of products and services.
- Its affordability and reliability have earned it a loyal customer base.
- That means setting up encrypted email with a new email address, encrypting messages with PGP, using a pseudonym, setting up an anonymous Bitcoin wallet, disabling Javascript in Tor Browser, researching vendors, and more.
- Plus, there’s a thorough vetting process for new buyers and sellers to keep the community more secure.
- AI has the ability to accelerate the scale and sophistication of cyber attacks and it’s starting to be incorporated into tools and services on the dark web.
While accessing the dark web isn’t necessarily wrong or illegal, it’s important to know how to navigate this part of the internet safely. Accessing the dark web isn’t like surfing the web everywhere else online. Silk Road quickly grew into the largest darknet market, handling hundreds of millions in transactions. But in 2013, law enforcement traced Bitcoin activity, monitored DPR’s forum posts, and exploited server vulnerabilities to identify Ross Ulbricht. He was arrested in a San Francisco library while logged in as site admin. To turn it on, just go to the “Settings” and then the “Tools” section of the NordVPN app and activate “Dark Web Monitoring.” In the end, it’s all about staying one step ahead.
Overall, Subgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments. Additionally, you can opt for Subgraph OS as a second option to Tor. In due course, the framework was remodeled and made public as a secure browser. An easy way to find content on the dark web is to receive a link from someone who already knows about it.
At first glance, Tor doesn’t look that different from your regular browser – it has a search bar, lots of quick-launch icons, the peeled onion icon smack in the middle of the screen. Well, now it’s time to fire up Tails and do a little bit of tinkering. Chill, because nobody will ever find a record of you ever fiddling around the darknet. Note that Tails’ installation package is the .img format, which means that you’ll need software capable of burning images on your thumb drive. Now, if you really want to take the physical storage devices out of the equation, you can use what I like to call a disposable operating system – easy to deploy and to get rid of if you by chance you run into any trouble. All you’ll need is an 8GB thumb drive, an installation package, and a couple of minutes to get things up and running.

Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them. Before your data reaches a site, Tor encrypts your connection and redirects it through a series of servers called “nodes” or “relays” to replace your IP address with each server’s address until it reaches the website. Most dark web marketplaces use cryptocurrencies like Bitcoin for transactions to help maintain anonymity. Once a buyer makes a payment, it’s usually held in escrow until they receive what they bought.
Use it to search the normal internet from the privacy of your Tor Browser. The three nodes separate your IP address from your destination and enable two individuals to communicate without either party, or any middleman, knowing who the other is. Needless to say, it takes your data much longer to travel this way, which means dark web links load slowly compared to indexed sites.