From stolen credit cards and hacked PayPal accounts to hard and soft drugs, pirated copies of all kinds, and weapons — there is nothing that is not offered on the darknet. Payment is usually made with Bitcoins, as the digital currency promises maximum anonymity and the payment flows are untraceable. Same people access the Deepweb in order to make use of the anonymity provided by Tor. Tor, which is also known as the onion router, allows you to conceal your true location in a way that provides anonymity and privacy. As soon as you connect to Tor, your web data is automatically tunneled through a number of “exit nodes” (random computers around the world). A modern, IP-enabled and secure communication and information network at the tactical level requires a reliable and stable network environment.
- Some content can be unmoderated, though, so it’s worthwhile to be careful while using this platform.
- During her academic years, she dedicated herself to assisting refugees fleeing war and violence in their home countries.
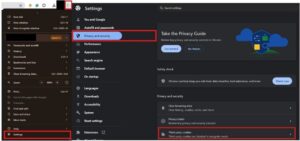
- To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network.
- You face significant risks when using dark markets, including scams where vendors take payment without delivering goods.
- KeyBase combines encrypted messaging with secure file sharing and identity verification.
Exploring The Use Cases Of Darknets & Dark Markets
However, it soon became a double-edged sword as malicious actors began to exploit its capabilities for illicit purposes. The internet’s underbelly – known as the Darknet or Blacknet – is a part of the internet that isn’t listed by conventional search engines. People are thus free to engage in criminal acts with a relatively small chance of being caught.
The Best Dark Web Links — Safe & Verified Sites In 2025
Alt Address provides disposable email addresses specifically designed for dark web use. This service helps protect your primary email when signing up for .onion services. I found it especially useful for testing new services without risking my main email address, though messages expire after 24 hours.

Escrow Services
After the Biker DLC, players can now purchase buildings for illegal drugs and counterfeit products manufacture, and distribute them through a darknet website called “The Open Road” where law enforcement cannot be notified of the player’s trade. The dark web contains numerous security risks, from malware to scams and illegal content. Thankfully, there are effective measures that keep you secure on the dark web and ensure you remain protected and anonymous while accessing .onion sites. Using a reliable VPN with Tor provides a way to improve security when accessing dark web links. The VPN encrypts your traffic before it enters the Tor network, preventing your ISP from seeing that you’re using Tor.
The challenge for concerned friends and family members is to educate themselves about these drug code words, so they can be more aware of what’s really going on around them. If you hear these terms or notice messages containing them, it may be time to look for other red flags and warning signs. When you familiarize yourself with these terms, you will be in a better position to help your addicted loved one. It might be a good idea to bookmark this page, so you can refer back to these drug street names. Individuals suffering from substance abuse often hide their habits by using slang to refer to specific substances.
Latest Data
If you access illegal content or participate in criminal transactions, you face legal consequences. The legality depends on your activities and your country’s specific laws regarding darknet use. Personal and financial data are commonly sold on dark markets, facilitating identity theft and fraudulent activities. The significance here lies in the potential damage to individuals and businesses.
What Is Cyber Threat Intelligence?
But it shows that some administrators aren’t content to make do with the current state of the market, which, although having grown significantly, still makes up a tiny percentage of global drug transactions. “We’re going to deny access to Russian users to the site, to avoid heat from the local law enforcement,” Mr. Evil continued, which further suggests that the site may be local to Russia. He also said that Chinese users would not be able to use the site, and vendors would be asked not to send products to those two countries. Its landing page includes a .onion dark web address, accessible only by using the Tor browser, but offers another “clearnet” link that can be accessed through a regular browser. In May, German police shut down Wall Street Market, a thriving marketplace that had more than 63,000 deals and 5,400 sellers, with over 1 million users worldwide. It was a resource-heavy operation, involving hundreds of separate investigations by five EU and US agencies.
Marijuana also significantly affects mental health and can lead to the worsening of ADHD, Bipolar Disorder, depression, and schizophrenia. It could continue to thrive, or it could face the same fate as Hydra, Silk Road, and AlphaBay. For now, it stands as a testament to the resilience—and the risks—of the darknet economy, reflecting the ongoing struggle between darknet operators and global law enforcement agencies. January 3, 2009 A man calling himself Satoshi Nakamoto “mines” the first Bitcoin, a form of untraceable cryptocurrency. Unlike previous digital currencies that failed because there was nothing to prevent users from literally copying their money, Bitcoin makes use of an innovative public accounting ledger that prevents double spending.
The Shift Toward Smaller, More Niche Markets
Financial fraud is common, and you have no recourse if transactions go wrong since these markets operate outside legal frameworks. Transactions within dark markets predominantly involve cryptocurrencies like Bitcoin, Monero, or Ethereum. These digital currencies provide a degree of anonymity, as transactions are recorded on a public ledger but do not directly link users to their real-world identities. To purchase illicit goods or services, users deposit cryptocurrency into an escrow system or directly to the seller, and the cryptocurrency is held until the buyer confirms the satisfaction of the transaction. For those still unaware, the dark net is a unique overlay network existing within the internet accessible using Tor. It isn’t visible to search engines, and for years it’s been a location of anonymized sites as well as illicit marketplaces.
It works in a similar way to Tor2Web, a system for accessing hidden services without Tor, Mr. Evil said. “Chemical Love,” a German language site, is accessible without any sort of anonymization technology. The slick homepage appears to list for sale all the drugs you might expect, including MDMA, methamphetamine, and cocaine.
A New Generation Of Networked UxV Systems
Singularity™ Threat Intelligence provides insights into adversary tactics and helps mitigate these risks before they impact your organization. Software firm Hyperion Gray put together a map showing all 6,608 dark web sites crawled during January 2018. Each screenshot is a site, and the content ranges from the nefarious to the noble.
Deployments require rapid and unpredictable movement of communication nodes and soldiers, making advanced network planning difficult. RIDUX is specifically designed to enable a dynamic, self-organising and self-healing network of networks. With the patented MeshFlow, seamless connectivity is possible even when soldiers move dynamically from one theatre of operations to another. Each node automatically recognises and identifies neighbouring nodes, providing a common communication link and information space.
We create solutions for the digitalization and networking of existing and new information and communication systems. In this way, we achieve effective interoperability with the existing digital and analogue radio technologies, but also the integration of new procurements. Darren Guccione is the CEO and co-founder of Keeper Security, the world’s most popular password manager and secure digital vault. Keeper is the first and only password management application to be preloaded with mobile operators and device manufacturers including, AT&T, Orange, America Movil and HTC. Keeper has millions of consumer customers and the business solution protects thousands of organizations worldwide.