Swensen said the most common dark web networks are Tor, I2P, and Freenet, but “Tor is, by far and away, the most popular.” But despite its many benefits, it’s sadly just a matter of fact that the dark web can be a dangerous place. Near total anonymity and a complete lack of regulation can easily attract criminality, and onion sites can harbor malware such as ransomware or spyware.
Most Popular Darknet Markets In 2025
A reliable, fast, and user-friendly VPN service offering lots of customizable options for privacy geeks. ActiveX and Java frameworks are susceptible to being exploited by hackers. Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe. We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch.
Describe what is your business or product about and how it is different. Here you will find over 75 unique, creative, and catchy dark business names that will help your business stand out from the crowd. Whether you’re starting a new business or simply rebranding an existing one, these names will give you the perfect place to start. With so many possibilities, you’re sure to find the perfect name for your business. We’re back with another video in our Webz Insider video series on everything web data. They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails.
Easy Steps To Access Dark Web On Your Phone Safely In 2024

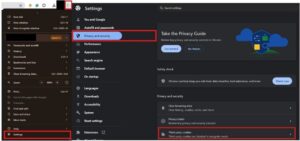
A virtual private network (VPN) is a good way to mask Tor activities. It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites.
What Is A Cloud Access Security Broker?
- However, there are some significant variances in the background despite the similarities.
- It is used by many for buying or selling items that are prohibited on the regular internet, like fake IDs, illegal drugs, and stolen data.
- DarkOde Reborn is a great darknet market where you can find anything you want.
- They can then trace the user, identify them as far down as their name and address, and act accordingly.
- First, let me explain that this article is intended for users who want to use the dark web for legal and needed purposes, such as finding censored news, blocked websites, and other much-needed services.
Here, you can exchange ideas, ask questions, connect with like-minded people through social networking, or share documents and media via peer-to-peer (P2P) file sharing. It’s not easy to find what you’re looking for on the dark web, especially if you want to do it safely. You should only ever access websites you know are safe because they’re vetted by websites or other sources that you already know are safe. Good starting points are the Onion Directory and the Hidden Wiki.
Browse The Dark Web Safely
This search engine will get you to the sites you need, though you can also go directly to dark web addresses if you know what they are, as with standard URLs. Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling. If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need. As noted by Andy Greenberg at Wired, while the deep web makes up approximately 90% of the internet, the dark web makes up only around 0.1% and is designed to provide anonymity for users and site owners. Government cyber teams can take such websites down, arrest the owners and then use the website to track and follow users that show activity on the website.
Best Dark Web Sites: Unseen Onion And Tor Links
Learn to fetch data, analyze content, and generate reports automatically. However, it’s very difficult and would require extensive resources, meaning that the average person’s identity is unlikely to be uncovered. Always tread carefully whenever crowdsourcing information on how to navigate the dark web.
The Marketplace As An Arsenal
Freenet was originally intended to provide a way to anonymously interact online, providing ways to communicate, exchange information and files, and to otherwise communicate incognito. The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web). The deep web is basically all the content that you can’t find using Google or Yahoo search.
Even with Tor and onion routing in place though, you’re not suddenly completely invisible and free to do whatever you want, without repercussions. Certain details of your traffic can be intercepted at the entry and exit points of the node, by the people running those nodes, if they know what they’re doing and what they’re looking for. You’re also open to threats like end-to-end correlation attacks, so while Tor is a lot more secure and private, it’s by no means completely safe. The core principle of the Tor network was first developed by U.S.
Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing. For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship.
Although some of these markets prohibit certain extreme content such as violence or exploitation, most operate with very few rules beyond ensuring the security and anonymity of their users. Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor…. The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities. This will help you to remain anonymous and secure at all Tor entry and exit nodes. It uses TrustedServer technology on the entire server network to wipe out your data after every session.
Is It Illegal To Access The Dark Web?
Simply accessing the dark web and using the Tor browser may already raise government suspicion. Anyone can access the dark web, and it’s not that complicated to do so. Just remember, if you want to explore the dark web, be very careful. This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware.