Sometimes, you might be hacked by using weak passwords or even just connecting to unsecured Wi-Fi on public networks. And in a world where almost everything we do is online, taking your digital privacy seriously is more important than ever. First things first, always use strong and different passwords for each account you open. Even after Silk Road went down, dark web marketplaces haven’t slowed down.
Cybersecurity Blogs And Forums
However, it is important to note that not all of this content is legal. Freenet is still an experiment designed to resist denial-of-service attacks and censorship. When you open your default browser, Freenet will be ready and running through its web-based interface. Note you should use a separate browser than the one you normally use to help ensure anonymity. Setting up I2P requires more configuration on the user’s part than Tor.
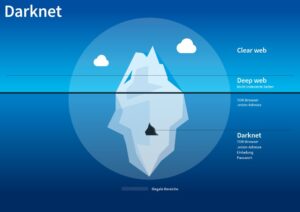
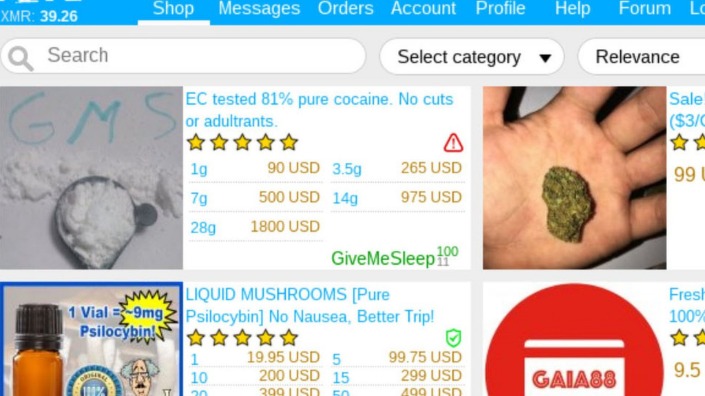
The dark web is a hive for criminal activity due to its anonymous nature and the fact that it is extremely hard to track down anybody who accesses it. In fact, research performed at the University of Kent in 2015 revealed that 57% of the dark web hosts illicit material. The dark web accounts for around 6% of the internet, and it is the secretive portion of the web where drug dealers, black hat hackers, hitmen, and human traffickers sell their wares or services.
What Is The Dark Web? How To Use Tor To Access The Dark Web
Neither ZDNET nor the author are compensated for these independent reviews. Indeed, we follow strict guidelines that ensure our editorial content is never influenced by advertisers. As previously mentioned, the dark web is not just used for criminal activities.

Is Accessing The Dark Web Illegal?
Tor Browser prevents someone watching your connection from knowing what websites you visit. All anyone monitoring your browsing habits can see is that you’re using Tor. As you might expect, Bitcoin is the top cryptocurrency being used on the Dark Web. Chainalysis says that $790 million worth of cryptocurrencies were used to shop in darknet markets during 2019. While some studies have claimed that illegal Bitcoin activity is as high as 44%. The dark web is content that exists on dark nets, which require specialized software (like the Tor Browser), configurations and authorization to access.
When the dark web is mentioned online, it is usually in tandem with criminal marketplaces and arrests made by law enforcement agencies. However, today’s most popular search engines — including Google, Bing, and DuckDuckGo — only index a portion of the internet. No longer restricted to dial-up, many of us now consider access to a stable high-speed internet connection a critical element of our daily lives. We pay our bills online, check our bank statements, communicate via email, find information, and maintain a presence on social media.
Tor is the most popular way to access the dark web, but it’s not the only option. Other privacy networks like I2P, Lokinet, and Freenet offer different layers of security and anonymity. Each tool works differently, and some are better suited for specific use cases than others.
Ways Small To Midsize Businesses Can Stay Safe In The Cloud
Selecting the optimal tool depends primarily on your individual privacy requirements, technical expertise, and the specific contexts in which you plan to access the dark web. Farwa is an experienced InfoSec writer and cybersecurity journalist skilled in writing articles related to cybersecurity, AI, DevOps, Big Data, Cloud security, VPNs, IAM, and Cloud Computing. Also a contributor on Tripwire.com, Infosecurity Magazine, Security Boulevard, DevOps.com, and CPO Magazine. Tor2door Market is among the largest dark net shops you must visit in 2025 if you’ve decided to visit such sites.
User-Friendly
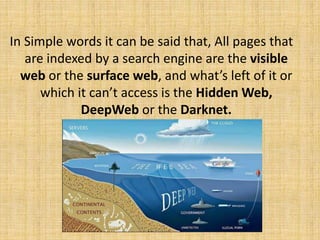
The open or surface web is what you access daily through search engines like Bing or Google. Before you even turn on the device, search engines have crawled through the web, looking for information, evaluating the sources, and listing your options. In order to understand the dark web properly, you need to understand that the internet is a huge and sometimes disorganized place.
Malicious Software
Use it to search the normal internet from the privacy of your Tor Browser. Torch is one of the oldest and most popular onion search engines on the dark web, serving over 80,000 requests per day. Torch is funded primarily through advertising—purchased in BTC, of course—which is why you’ll find the front page blanketed with old-school banner ads of dubious origins. Learn how to safely access the dark web with this comprehensive guide for beginners.
Popular Dark Web Search Engines And Sites
We love it because of its simplicity, which, as you saw, lets you visit the dark web in seconds. NordVPN’s NordLynx protocol is more than secure, with a certified no-logging policy that guarantees no logging and storing of your sensitive data. For one, the VPN can’t see your online activities because of VPN encryption. Plus, the ISP won’t see that you’re using Tor, which is excellent.
- Your Internet service provider, or ISP, is your gateway to the Internet.
- When you know what to expect, you’re less likely to fall for a trick and should be able to keep your identity safe.
- Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem.
- There are a lot of misconceptions about the dark web online and in popular media.
- Another sensible general rule to follow on the dark web is to not buy anything there.
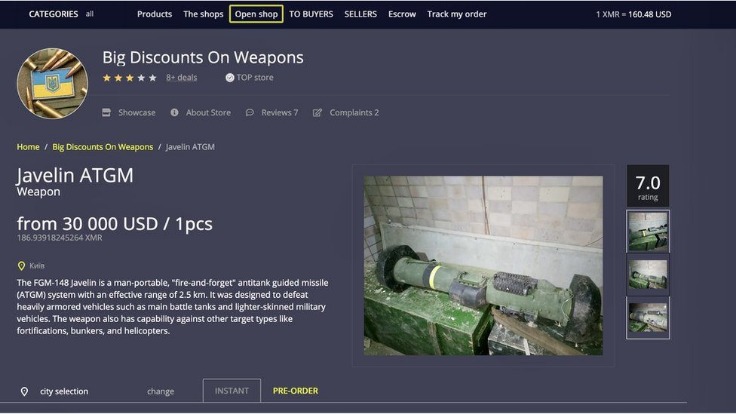
In many countries, strict laws limit who can legally buy, own, or carry firearms. The site gives out free samples of the stolen data every now and then to gain more customers. With its fast rise to fame and focus on money fraud, it’s no surprise that cybersecurity experts are keeping a very close eye on this one. Next up is Abacus, another newer market that has already made a massive name for itself, especially following AlphaBay’s closure.
Dark Web Links: The Best onion And Tor Sites In 2025
It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media). As always, use Tor Links with care, as it includes onion links to dubious or illegal activity. The Tor browser uses the Tor network, which was developed in the mid-1990s by US Naval Research Laboratory employees.
It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder. In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. Accidental leaks at the Tor entry nodes can potentially expose your IP address. ExpressVPN is an excellent choice for Tor and accessing the Dark Web.
Reputable organizations, security researchers, and privacy advocates provide a wealth of insights, tutorials, and software to help you explore safely and responsibly. Below are some trustworthy starting points and authoritative references. By understanding the hazards you may face in the Dark Web and implementing the precautions outlined above, you’ll be better equipped to minimize your exposure to scams, malware, and identity risks. Remember that good judgment, ongoing education, and constant vigilance are your most powerful tools for maintaining a safe and private Dark Web experience. Among the many benefits of using a VPN vs a proxy or Tor is that it provides full encryption for all the data you send and receive online.