It is easily accessible by the general public and requires no special configuration. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. Blockchain even has an HTTPS security certificate for even better protection.
Ways Small To Midsize Businesses Can Stay Safe In The Cloud
Facebook’s onion mirror allows people to access it in countries that block the platform, allowing people to connect across digital borders. That said, the social network’s data collection and tracking practices may seem at odds with many of the principles motivating dark web users. Concerns about how Meta treats user data have led many people to delete their Facebook profiles or at least limit their social media presence. Beyond the legal aspects, there are ethical considerations to weigh. At the same time, these networks can also facilitate exploitation, hate speech, and other harmful activities. Laws pertaining to anonymity and the use of privacy-enhancing tools vary widely from one country to another.
- As dark web websites are not moderated, they can host a wide range of malware, such as ransomware, keylogger, and remote access Trojan.
- They have an onion site as well, presumably to allow access to the website’s content in countries that aren’t so friendly to the notorious intelligence agency’s …
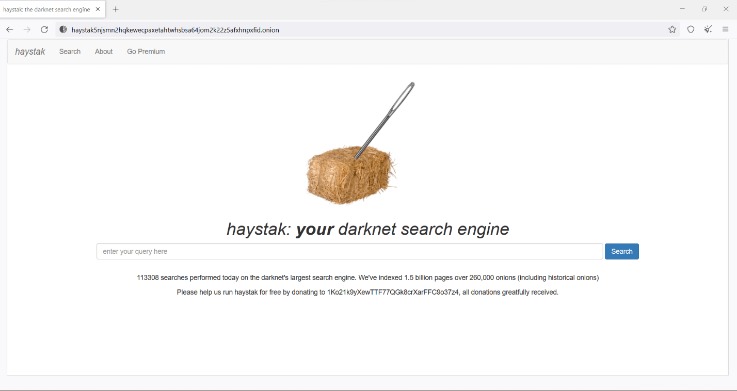
- When you search a term (or query) in a web browser, the search engine combs through the database to find relevant results and serves them up on SERPs.
- While no approach guarantees complete safety, a careful and skeptical mindset serves as one of your most valuable tools on the hidden internet.
- SecureDrop stands out as the leading platform for secure document sharing used by major news organizations.
So take this guide as you explore where to go on the Tor Browser without risking your online security. Dark web websites don’t bear Internet Corporation for Assigned Names and Numbers (ICANN) domains, such as .com. They use a scramble naming structure that combines a string of letters and numbers to create URLs that are impossible to remember. If your incoming traffic passes through a node run by cybercriminals, they could inject malware into the response code. If your device is unprotected, you could be a victim of malware or a hacking attack.
Government Surveillance
And, with an automatic kill switch that guards against unexpected exposure if the connection drops, you can enjoy powerful privacy protection as you navigate even the darker corners of the web. Proton Mail is an anonymous email service that operates an onion site. If you want to learn all about privacy protection or cryptocurrency, the dark web has plenty to offer. There are a variety of private and encrypted email services, instructions for installing an anonymous operating system and advanced tips for the privacy-conscious. With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with.
II Security And Anonymity On The Dark Web
It has a vast library of over 1.5 billion indexed pages that lets you find whatever you are looking for. However, the threat of clicking on the wrong link always remains, so be cautious while you use it. For individuals in locations facing strict restrictions or those under oppressive governments, ProPublica is the perfect platform to share their stories.
Structure Of The Internet: Surface Web, Deep Web, Dark Web
Search engines on the dark web are a bit of a contradiction because dark web sites by definition are not indexed by traditional search engines. Safe browsing on the Hidden Wiki requires a combination of technical precautions and behavioral discipline. Always access the Hidden Wiki through the official Tor Browser, never via a standard browser. Disable JavaScript and other potentially risky browser features unless necessary, as they can be exploited to reveal your identity. Avoid downloading files or opening attachments from unknown sources, as these can contain malware. Use strong, unique passwords and enable two-factor authentication where possible.
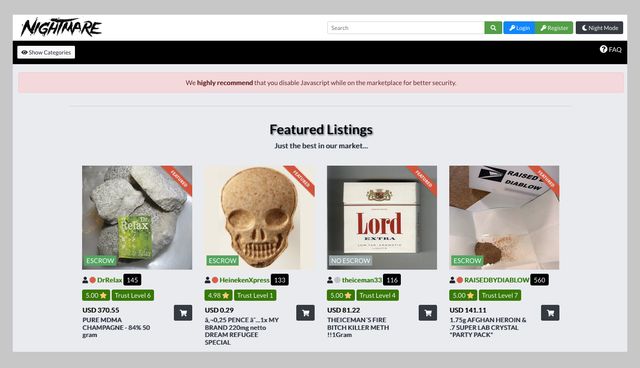
The site doesn’t require an email verification, though it offers all the features and security that you want in a dark web marketplace. Onion sites are far safer to use as they are hidden deep within the deep web. Also, since users can only access them using the Tor browser (with its high-end encryption), users can be rest assured their identities and locations remain hidden.
Use A VPN
However, it’s up to us to take control of our personal privacy in a world of bulk data collection, surveillance, and personalized ad tracking. There are many legitimate uses for dark web services and communication. Market admins use AI to detect scams, fake reviews and phishing links, while law enforcement deploys machine learning to map vendor reputations and analyze seizure data. In parallel, threat actors have begun using LLMs to auto‑generate malware listings and evade keyword filters, accelerating both growth and complexity. You’ll learn how it differs from the surface and deep webs, how Tor and similar networks maintain anonymity, and why some activities cross legal lines.

Never Share Personal Information
Criminals prefer the dark web because it offers anonymity like never before. But as long as you don’t knowingly engage in illicit activity on the dark web, you are completely fine. The marketplace has an intuitive interface and offers powerful search tools that make it easy for you to find products from both local and international sellers. All vendors are vetted before they are allowed to sell, so it makes sure of trust and quality. Few countries operate with strict censorship on citizens’ internet access, preventing them from getting information in or out. BBC is the most popular news source and is the best example of restrictions on International media.
- Don’t click on suspicious links, be skeptical of what you read, and avoid dark web marketplaces if you don’t want to stumble on illegal activity or content.
- Simply put, accessing and browsing the dark web is perfectly legal.
- However, because it’s almost completely anonymous, there are a lot of illegal images, information, products, and services on the dark web.
- Many free VPN providers lack basic security features and track your online activity, so they don’t offer much privacy.
- All our revenue comes from Proton customers who upgrade for more storage and premium features.
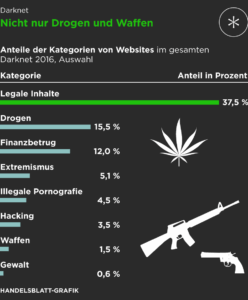
Darknet Markets
If you search for obscure copyright-free ebooks on Google, you’ll have to click through several pages to find a result that provides a download link. However, it’s still a great way to get a taste of what’s available on the dark web without exposing yourself to the inherent risks of using the dark web. Before exploring, you should first know how to avoid dangerous content on the dark web.
Best Dark Web Websites
Deep web refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google. Deep web content includes anything behind a paywall or requires sign-in credentials. It also includes any content that its owners have blocked web crawlers from indexing. However, there are plenty of legal and legitimate online activities that require privacy and anonymity. The dark web is used by journalists, whistleblowers, and political activists who need the protections that it offers. Anything you need to do that has to be off the books to some extent, for noble or ignoble reasons, can be done on the dark web.
Cybersecurity Best Practices For Protecting Your Digital Assets
Hacker services against banks and other financial institutions are offered there. Lastly, the dark web is also used by activists and revolutionaries (like Anonymous). The dark web serves as a platform where activists can organize gatherings in secret, without the fear of giving away their plans or position to the government. Especially for these people, the dark web is the perfect platform to communicate and publish information without having to worry about imprisonment or any other form of retribution. The purpose was to protect U.S. army soldiers and agents in the field, but also politicians who held secret meetings and conversations, which contained the highest security measures. Those who access the dark web do so via the Tor (The Onion Router) browser.