In addition, the content on the pages don’t need any special or custom configuration to access. It might sound weird that Google doesn’t index these pages, but it does carry some logical sense. Google’s purpose is to show the most relevant information to all of its users quickly and easily.
How KELA Cyber Supports You In Darknet Monitoring And Risk Mitigation
It uses PGP encryption, two-factor authentication, and OPTP authentication to ensure users’ security. Cypher marketplace has been on the list of the best dark web shops for a while and deals with the business of a variety of products and services. The shop accepts payment through Bitcoin and Monero, while some vendors accept the coins. As these marketplaces keep changing, it is critical to stay on top of the main platforms on the dark web worth monitoring.
Budget, Financial Reporting, Planning And Performance
We have built the interactive maps and conducted the preliminary visualizations to construct the hypothesis. This provided a baseline understanding of the spread and prevalence of various drugs. Beyond drugs, there are now ever-growing examples of generative AI being used for sexual deepfakes across schools and even of public figures, including the recent case of NRL presenter Tiffany Salmond. Usually these products are sent to the buyer by post and money transferred to the seller through the escrow system.
Darknet Market Links
Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser.
Use Cryptocurrency For Transactions
It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in. In exploring the top 10 dark-web marketplaces in 2025, we’ve examined their core operations, diverse use-cases, inherent risks, and evolving trends. While these marketplaces continue to serve legitimate purposes, such as enabling secure communication and privacy protection, they also remain hotspots for illicit activities and cybercrime. You can use dark web monitoring tools, such as NordVPN’s Dark Web Monitor, to check if your data has been leaked.
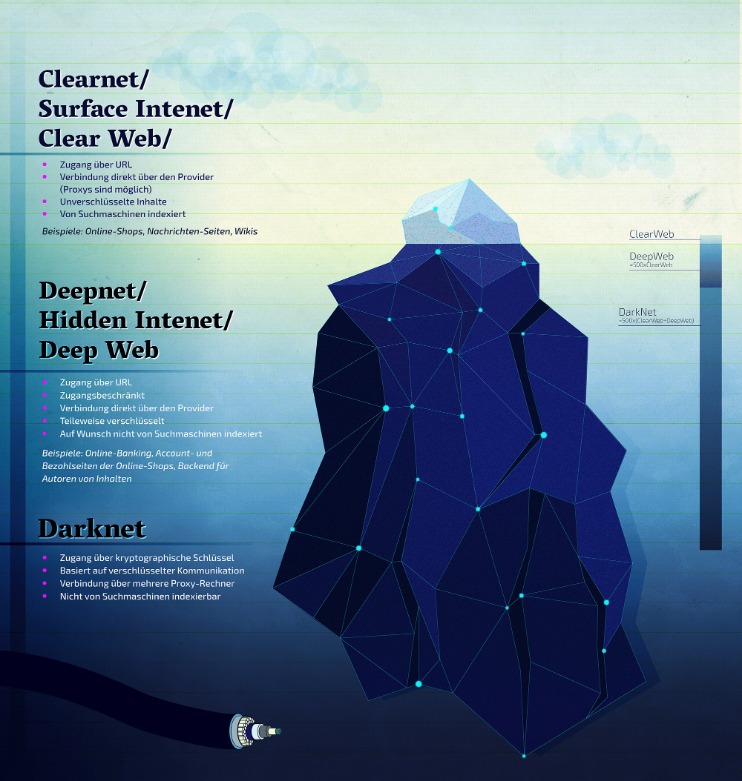
- When you search for something on Google or Bing, you’re using the clear web.
- If you want more peace of mind, NordVPN has a dark web monitoring tool you can consider using.
- When you install a VPN, all of your activities on the dark web will be hidden from unwanted snoops from your ISP or the FBI.
- He was formerly the Chief Financial Officer and a principal shareholder of Apollo Solutions, Inc., which was acquired by CNET Networks.
Then, you can set up 2FA (two-factor authentication) for that extra touch of security in case someone somehow figures out your password. If you ever have to connect to public Wi-Fi, make sure to use a VPN to keep your browsing safe and private. According to a recent trend, the dark marketplaces faced a decline in revenue. Chainanalysis, a blockchain analysis firm, conducted research that shows that the revenue decreased from $3.1 billion (2021) to $2 billion (2024). Like ransomware, criminals can buy software and inject your devices with viruses. With it, they can spy on people, steal their sensitive data, or secretly control their devices.

Exploring The Use Cases Of Darknets & Dark Markets
The dark web has flourished thanks to bitcoin, the crypto-currency that enables two parties to conduct a trusted transaction without knowing each other’s identity. “Bitcoin has been a major factor in the growth of the dark web, and the dark web has been a big factor in the growth of bitcoin,” says Tiquet. There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks.
Payment Methods Overview
These digital currencies provide a degree of anonymity, as transactions are recorded on a public ledger but do not directly link users to their real-world identities. Empire Market is a dark web shop that resembles the AlphaBay marketplace. Its look, design, options, and interface are exactly the exact copy of its competitor, but everything else, including buyers, vendors, and servers, is different.

Instead, I2P uses its own brand of hidden sites called “eepsites”. To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network. This browser enables access to websites with .onion domain extensions, which are specific to the Tor network. These addresses cannot be resolved by conventional DNS servers, contributing to the hidden nature of darknets.
Unlike Bitcoin, which records every payment on a public ledger, Monero conceals all transaction details by default, which makes them nearly impossible to trace. Navigating dark web marketplace links can be risky; however, with the right tools, you can explore safely. Your ISP, and possibly the authorities, may decide to start monitoring your activity more closely to look for threats or illegal activity. That’s why we always recommend using a VPN over Tor—even if you feel you have nothing to hide.
For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. One option is to try DuckDuckGo’s .onion version, which is great for privacy.
Transactions within these marketplaces typically leverage cryptocurrencies—most commonly Monero, Bitcoin, and privacy-centric digital currencies developed specifically to enhance transaction anonymity. Monero, in particular, has become the preferred cryptocurrency on the dark web in 2025 due to its advanced privacy mechanisms, which obscure transaction histories and wallet balances from public view. Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation.

My dedication to continuous learning fuels my passion for delving into the complexities of the cyber world. And if you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics. When you’re done surfing or shopping on the dark web, don’t forget to shut down Tails.
All your traffic is automatically routed through the Tor Network. Ensure you download the Tor Browser from the official website to avoid downloading malware, spyware, or other viruses to your device. As long as users take the necessary precautions, no one knows who anyone else is in the real world. Users’ identities are safe from the prying eyes of governments and corporations. The MITRE ATT&CK framework provides a comprehensive view of adversary tactics. Singularity™ Threat Intelligence provides insights into adversary tactics and helps mitigate these risks before they impact your organization.
Are Sites On The Dark Web Illegal To Use And Visit?
This was the initial framework for anonymous communication and file sharing. Immediately change your passwords, enable two-factor authentication, and notify your bank or credit card provider if the leaked information includes your financial data. You should also consider freezing your credit to prevent identity theft.