
The dark web remains a small, hidden part of the internet with strong ties to illegal activities and should be approached with caution. Tools that can profile users and analyze their relationships are vital in understanding criminal networks operating on the dark web. User profiling can reveal repeated behavior, while link analysis can demonstrate relationships between different entities, be it individuals, websites, or transactions. There are 1,208,925,819,614,629,174,706,176 possible site addresses on the dark web, and that’s just counting Tor .onion sites. It wouldn’t be possible to check each one to see if they’re online and then also look for your data on them. The identities and locations of users are anonymized through a layered encryption system, a traffic anonymization technique known as onion routing.
The New York Times — Globally Recognized News Coverage
Since you cannot access a library of dark web links using the regular Internet, you can check out platforms dedicated to indexing these sites, like The Hidden Wiki. Awazon Marketplace is the leading dark-web marketplace that claims to provide a secure destination for anonymous trading. The site also uses strong encryption to protect against cyberattackers, such as anti-DDoS protection. It doesn’t use JavaScript, which goes a long way toward keeping you anonymous. Ahmia is a safe alternative search engine for users who prefer the dark web.
Bitcoin Services
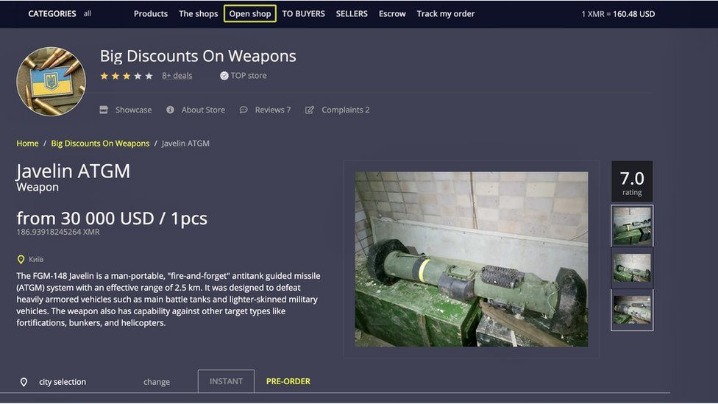
The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web. For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. However, there’s a chance you may run into illegal activity on all but the best onion sites.
What Are Dark Web Websites?
Most internet users want to use the dark web safely, but it’s still important to be careful when using any onion browser. On the other hand, the dark web hosts marketplaces and forums where illegal goods and services—such as drugs, weapons, and stolen data—are traded, making it a hotspot for criminal activity. Despite its negative reputation, not all activity on the dark web is malicious; some users rely on it as a tool for freedom of expression or to circumvent restrictions.
A Complete Guide To Data Breaches
Through Tor, users can access a number of dark web websites, including mirrored versions of surface web sites such as Facebook and The New York Times. For those who really want to explore the dark web, several pages called the Hidden Wiki serve as a directory of links to other .onion sites. The dark web is a part of the internet that isn’t indexed by search engines. You’ve no doubt heard talk of the “dark web” as a hotbed of criminal activity — and it is. Researchers Daniel Moore and Thomas Rid of King’s College in London classified the contents of 2,723 live dark web sites over a five-week period in 2015 and found that 57% host illicit material.
Tor (The Onion Router)
It hosted over 7,000 .onion categorized links to make surfing the web easier. One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is online. After more than a year of no updates, the site admin shut it down, reasoning that he couldn’t keep the list of onion links up-to-date. However, most are outdated and have not kept up with the changing landscape. For example, DuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question.
- The best Tor sites are under constant threat of closure, including Tor directories like the Hidden Wiki, so having a backup in case one goes down is handy.
- The dark web may be the Wild West of the internet — a place without rules, gatekeepers, or censorship — but there are still reasons to visit.
- The dark web is home to the internet’s hidden sites, services, and products — some innocent, others downright dangerous.
- It’s the part of the internet that we’re all familiar with and use on a daily basis.
- Thankfully, there are effective measures that keep you secure on the dark web and ensure you remain protected and anonymous while accessing .onion sites.
I think it’s safe to say that these are unsanctioned exploits, all the more reason to boast them on the dark web. I have to admit to having a soft spot for Tunnels, an onion website about underground “urban” exploration. Apart from having that “As above, so below” vibe, Tunnels is a great source of info for users who are into dark urban history. The website contains pictures and videos of various cavern-like structures, shafts, and possibly escape tunnels.
- Traders cash in on stolen credit card data dumps, initial access points to vulnerable systems, credentials, and intellectual property belonging to companies compromised during cyberattacks.
- It’s an interesting resource that translates Tor internet traffic levels into easy-to-digest stats.
- Your ISP, and possibly the authorities, may decide to start monitoring your activity more closely to look for threats or illegal activity.
- Formerly known as Archive.is, it is one of the best onion sites on the dark web.
What Is Onion Routing?

The dark web is a subset of the deep web that is intentionally hidden, requiring a specific browser—Tor—to access, as explained below. No one really knows the size of the dark web, but most estimates put it at around 5% of the total internet. Again, not all the dark web is used for illicit purposes despite its ominous-sounding name. Harmful relationships can isolate people from their family and friends. And, unfortunately, technology plays an increasingly prominent role in how abusers control their victims through various forms of stalkerware. Making it easier for cybersecurity teams to stay on top of potential threats.
DuckDuckGo is the default search engine inside the Tor browser, and once you turn on the Onionize toggle switch in the search box, you’re able to use it to find dark web links. These typically come with “.onion” after them, rather than something like “.com” as on the standard web. This will help you to remain anonymous and secure at all Tor entry and exit nodes. It uses TrustedServer technology on the entire server network to wipe out your data after every session. A virtual private network (VPN) is a good way to mask Tor activities.
Due to the privacy-forward ethos of the Tor project, Tor Metrics stresses that the data it collects must not undermine the anonymity or security of the network. ProtonMail is a Swiss-based encrypted email service that doesn’t require personal information when you sign up. ProtonMail’s end-to-end encryption makes it one of the best onion sites for easy-to-use, secure, anonymous email. The BBC and other well-known news services are blocked in some parts of the world.
Legal Activities
Keybase is a dark web messaging application that functions much like Signal and WhatsApp, except it is secure and private. This service lets you create your unique domain name with the letters or words you prefer. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page.
The best VPN options are paid-for and subscription-based, as many free options will either throttle your speed or collect your data. ZDNET’s recommendations are based on many hours of testing, research, and comparison shopping. We gather data from the best available sources, including vendor and retailer listings as well as other relevant and independent reviews sites. And we pore over customer reviews to find out what matters to real people who already own and use the products and services we’re assessing.
The dark web now brings together wannabe and seasoned hackers from around the world and equips them to magnify their efforts. Each relay decrypts a layer of encryption to reveal the next relay in the circuit and passes the remaining encrypted data on. Open-source software design to syndicate data over a variety of anonymous and non-anonymous computer networks. Decentralized peer-to-peer network built using VPNs and software/hardware BGP routers. It does not try to establish anonymity for participants and is used to explore routing technologies used on the Internet. Search engines work by collecting, parsing and storing data about the pages they visit, enabling every day people fast and accurate information retrieval.



