The Tor Browser routes your internet traffic through a network of servers, making it difficult for anyone to track your online activity. If you start to wade into Dark Web waters, it’s not as much about safety as it is about legalities. If you stay in Deep Web territory, there is plenty you can do where online safety isn’t a significant concern. Understanding how to use Tor is one of the best ways to familiarize yourself with the Deep Web and what you can really do. Sites like WorldCat help bring the Deep Web that revolves around indexing databases to the forefront.
A Virtual Private Network (VPN) encrypts your internet traffic before it reaches the Tor network, adding another layer of security. If you plan to use NotEvil, prioritize these essential safety measures to protect your identity and data while navigating the dark web. If you’re looking for more cybersecurity-related content, check out the best Cybersecurity YouTube Channels to stay updated on the latest trends.

How Do OSINT Professionals Monitor Criminal Forums?
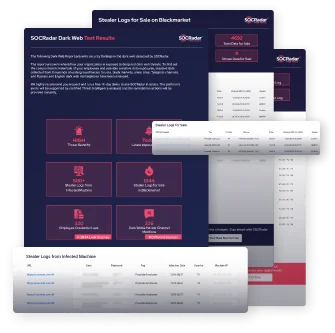
Part of its service is the threat intelligence solution that automatically scans and updates the databases with new information collected all around the web. This tool monitors extensive dark web resources for exposed credentials, intellectual property, fraudulent activities, stolen data, VIP and executive threats, and more. It inspects underground marketplaces, Telegram, IRC, Tor, I2P pages, forums, and paste sites and sends alerts to notify the affected organizations.
Frequently mimicked by clones and scams, the “authentic” Hidden Wiki requires verification via trusted Tor forums (e.g., r/onions on Reddit). Its simplicity and structure make it ideal for beginners, but its lack of keyword search limits depth for advanced users. Visit a known .onion site (e.g., Ahmia’s .onion link) to ensure Tor is working. Password managers can help manage your credentials without compromising security. In addition, many dark web websites are configured to block or mislead regular crawlers. And since these sites require access through Tor, they can’t be reached over a normal connection.
Actionable Threat Intelligence
However, constant online security monitoring is typically a paid service offered by a certain provider (including the ones we’ve listed above). Identity Guard is owned by Aura and is one of the best identity theft protection solutions on the market today. Identity Guard uses your email address to scan the dark web for any compromised data.
What Makes A Good Tor Search Engine?
Before exploring, you should first know how to avoid dangerous content on the dark web. Veridian Software is the company behind the now-dead portal for historical newspapers, Elephind. If you loved Elephind and want an alternative, you’ll be happy to know that all of its library is still accessible via Veridian’s website. Not everything on the web will show up in a list of search results on Google or Bing; there are numerous places that the sites’ web crawlers cannot access. Recon is used to find information about darknet vendor profiles and monitor their activity. If you’re not using Tor, a VPN, or proper anonymity tools, there is a risk of being tracked.

How To Stay Safe While Using NotEvil
- Unlike the surface web, dark web search engines have no reliable mechanisms to report or take down malware-hosting websites.
- While not a monitoring tool in and of itself, its utility in dark web investigations makes it a key resource for cybersecurity professionals and law enforcement.
- It is not a crime to access uncensored news or a site you want to use in case of restrictions or outages due to our topic.
- It is worth noting that for clearweb, web browsers like Brave and Antidetect browser
Brandefense provides tools to monitor and avoid these risks, ensuring compliance with legal and ethical standards. However, this intelligence and creating a complete picture of the threat environment can be complex and requires a thorough understanding of the dark web and how to conduct an investigation. When using the Dark Web, it is essential to avoid sharing personal information, use strong passwords, and steer clear of sites involved in illegal activities. Additionally, using a reliable search engine like Ahmia can help avoid dangerous sites. Ahmia offers a user-friendly interface and curates a list of safe .onion sites.
How Can I Safely Access The Dark Web?

It’s a great starting point for newcomers to the dark web, ensuring users avoid dangerous or illegal sites. ZeroFox Dark Web Monitoring is another software that aims to simplify the process of surfacing risks from the dark web. Continuous monitoring of compromised credentials, employee personal information, or sensitive corporate intellectual property is just the start for ZeroFox.
Hidden Wiki
Haystak is one of the dark web search engines designed for the Tor network. The search engine claims to have indexed over 1.5 billion pages which includes more than 260,000 websites, Haystak indeed would stand out to be a resourceful engine on the list. It’s specifically designed for privacy, routing your connection through the Tor network to hide your IP address and encrypt your traffic. Built-in features like script blocking and anti-tracking ensure a safer browsing experience.
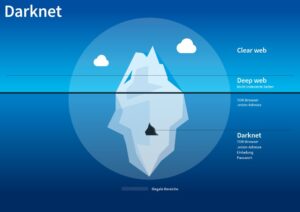
Specialized dark web monitoring services continuously scan the dark and deep web using tools specifically designed for that and extensive indexing methods to look for compromised data. Tor search engines enable users to access the dark web by routing web traffic through a decentralized network of nodes. The Tor Browser conceals IP addresses and browsing activity, ensuring anonymity.
Discover how to use a darkweb search engine safely while enhancing your online privacy and security. Dark web engines like NotEvil index these domains exclusively, allowing keyword-based discovery of sites that surface engines can’t reach. They’re essential for secure access but require verification to avoid phishing mimics. Privacy advocates also use them to explore anonymous services (e.g., encrypted email) without surveillance. Stick to filtered engines like DeepSearch to focus on ethical content while avoiding illicit areas. These newcomers focus on user trust and cross-network support (e.g., I2P), but verify their .onion stability via communities.
Yes, DuckDuckGo has a .onion version that works through the Tor browser for anonymous searching. DuckDuckGo offers a .onion version with privacy-first results from both surface and dark web. It’s not filled with malicious actors looking to sell or data or steal from you. Dashlane offers 3 different plan tiers to meet your specific security needs.
Although transparency is an advantage in itself, at the same time, it can also prove to be quite a disadvantage. Threat actors can research the openly published source code to find vulnerabilities and exploit them, a thing that may harm the organization and the data. Setup, configuration, and subsequent maintenance may require highly skilled personnel with the time to devote to operating and maintaining this particular tool. Sometimes a free dark web scan tool does not integrate with existing systems or other proprietary software.
While dark web search engines are essential for accessing the dark web and monitoring potential threats to your business, they are not without their own risks. Each search engine opens the door to potentially harmful content, making caution a necessity. While it doesn’t index dark web content, it’s the default search engine on the Tor Browser because of its strong privacy features and lack of tracking. For searching within the dark web, specialized tools like Torch are better, as they specifically index .onion sites and hidden content. The World Wide Web Virtual Library is one of the oldest and most reliable online resources.
Torch is a leading dark web search engine known for its extensive index of .onion sites. Torch stands out for its commitment to user privacy, as it doesn’t store search history or collect any user data, ensuring higher anonymity. It also provides uncensored search results without displaying ads, which reduces the risk of encountering malicious links or suspicious sites. Like traditional search engines, dark web search engines also use web crawlers, but not the same ones. The difference is that they are specialized web crawlers designed to operate within the Tor network and index .onion sites. However, the process is slower and much more complex because of the encryption, anonymity protocols, and the unstructured nature of many dark web sites.