Their URLs (aka dark web links) have .onion as the domain, instead of the common surface web domains like .com or .net. By closely monitoring market movements, we offer in – depth analysis that empowers businesses and individuals to make strategic decisions. In the online shopping space, we help retailers optimize their platforms and consumers find the best value. When it comes to digital finance and cryptocurrency, we demystify complex concepts, guiding our audience towards sound investment and financial management choices. Once installed, you can use it similarly to any other browser, but with the added benefit of accessing .onion websites and browsing anonymously. From the latest news on Darknet Markets to tutorials on how to access certain .onion sites, DeepDotWeb offers a comprehensive resource for all things related to the Tor network.
Escalating Threats In The Middle East
Depending on your preference, you can find links in well-categorized groups. These categories include email providers, news sites, privacy, and commercial services. Ruheni Mathenge specializes in writing long-form content dedicated to helping individuals and businesses navigate and understand the constantly evolving online security and web freedom worlds. Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across.
Image Hosting — Upload & Share Images
But finding reputable onion links and dark web websites can be a challenge. That’s why we took the guessing work out of it for you, and made this list of the best dark web sites you should check out. Although most dark web search engines emphasize privacy, not all follow through. Some may log search history, contain hidden scripts, or other elements that can jeopardize user anonymity. Always choose search engines that uphold user privacy and avoid those that collect data or present intrusive scripts. Unlike the surface web, dark web search engines have no reliable mechanisms to report or take down malware-hosting websites.
Subscribe To The Blog Newsletter

While many users turn to the dark web for legitimate reasons, such as journalists or activists seeking to avoid censorship, it is also known for illegal activities. Many dark web search engines offer uncensored search results, increasing the likelihood of encountering illegal content such as abuse material or hidden services. Even if you are not searching for such content intentionally, spam links and vague search queries can direct you toward harmful content.
How To Stay Safe While Using Onion Websites
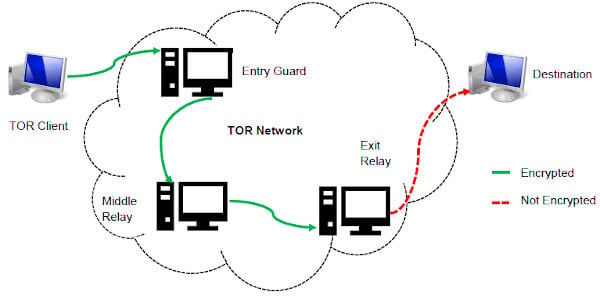
The best way to stay up-to-date with the latest happenings is to use an open-source and community-oriented news aggregator like SoylentNews. Users can submit their stories from anywhere in the globe and even engage in insightful conversations on public discussion forums. Dark web links operate on a system of layers (like an onion) where each layer encrypts traffic as it passes through multiple relays. The websites also contained detailed advice on how to avoid detection by law enforcement.
Use Norton VPN to encrypt the data you send and receive and surf more anonymously. By following these precautions, you can explore the dark web with a greater degree of safety and security. Ahmia promotes transparency by being open-source and allowing contributions. Its operations focus on respecting user privacy and maintaining anonymity through the use of the Tor network. Since 2020, 2easy has sold massive stealer logs with sensitive data like passwords, bank cards, and initial access credentials.
What Kind Of Information Can I Find On Dark Web Search Engines?
Whether you’re exploring it out of curiosity or for legitimate personal reasons, it’s essential to approach this hidden realm with the right knowledge, tools, and security measures. While it may have a reputation for seedy and dangerous content, many dark web websites are legitimate and useful resources. Keep reading for a rundown of the best dark links you might want to check out. Since the dark web isn’t indexed by standard search engines, sites like Ahmia act as modified directories to help users discover onion sites. In some ways, dark web websites offer more browsing freedom, but the lack of safeguards can leave you exposed to hackers, malware, and other online threats, like viruses or other malware.
- Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble.
- However, it works best in real-time since the file transfers are interrupted if you turn off your system.
- WeTheNorth is a Canadian market established in 2021 that also serves international users.
- After all, it enables users to connect and communicate with each other from around the world.
Useful Links

Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. Believe it or not, some dark web marketplaces have pretty advanced systems for building trust. Sellers often need to pay a deposit to prove they’re serious, and they build their reputation through positive reviews. These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down.
Where illegal activities such as weapons sales, drug trafficking, and other criminal activities occur. As cryptocurrencies are decentralized, there are reasonable concerns about the use of cryptocurrencies in facilitating criminal activities on dark web websites. While the Hidden Wiki is a popular directory for accessing dark web resources, it is far from being completely safe by default. The dark web environment is notorious for hosting scam links, phishing clones, and honeypots designed to deceive visitors. Scam links may direct users to fraudulent marketplaces or services promising deals or products that never materialize, resulting in lost money or stolen credentials. Phishing clones are fake copies of legitimate dark web sites or marketplaces, created to harvest login details and personal information from unsuspecting users.
Another evolution in cybercrime is the motivation of the cybercriminal. While a threat actor doesn’t generally care about the type or size of the organization they target, their motivation generally, although not always, points to the victim. Understanding these motivations helps to plan effective cybersecurity strategies. Malware is any software that is designed to harm or exploit a computer system. Dark web hackers often use malware such as keyloggers, ransomware, and trojan horses to access sensitive information and cause damage. Let’s look at some of the key stats and trends that illustrate what the dark web is today, including its rate of growth and in which countries much of its activity takes place.
Don’t Be The Next Dark Web Statistic: Protect Yourself Against Cybercrime And Stolen Data
And when you are carrying out transactions on the dark web websites then this increases the risk of scams. For some people, anonymity is not a priority, they are more concerned with carrying out legal transactions through their saved-up cryptocurrency. In the previous point, we talked about the creation of an international regulator authority. Another reason that such an organization is required is that cryptocurrencies can be transferred across borders quickly and easily, making it difficult for regulators to track money flows.
Best Free Firewall Software In 2025

They usually accept cryptocurrencies, such as Bitcoin, which keeps transactions secret. There are no visible ads or trackers, and the design is often very simple. The cybersecurity challenges seen in 2024 highlight the dynamic and ever-evolving nature of cyber threats. As cryptors, loaders, and stealers become more sophisticated, and underground markets remain resilient, organizations must prioritize robust cybersecurity measures in 2025. This shift will likely drive forum operators to introduce features like automated escrow services and enhanced anonymity to attract users. Black traffic schemes—malicious landing pages promoted via deceptive ads—remained a constant threat.
This setup can help prevent network-level surveillance and reduce risks in environments where Tor use might be flagged or restricted. Choose a trustworthy VPN service that has a strict no-logs policy and supports connection without DNS leaks. Avoid free VPNs as they often lack adequate security or monetize user data.



