Ultimately, your safety on these sites is your responsibility, so please keep your wits about you as you navigate. Because the Hidden Wiki aggregates many links, it often contains outdated or malicious URLs disguised as legitimate ones. This makes blindly clicking links risky and requires users to exercise caution when navigating these directories.

It’s for the good that these sites are not available for the general internet user. The Daniel site also had a status check feature that updated users on which sites were active. Unfortunately, the site’s admin could not keep up with the time demands and has taken down the links on the site as of August 2023. In addition, Haystak offers a premium plan that allows deeper search, email alerts, and access to historical content. It has a vast library of over 1.5 billion indexed pages that lets you find whatever you are looking for.
How Do I Verify An Onion Link Is Safe?
For these reasons, it’s a good idea to safeguard your online activities with NordVPN while using the dark web. The platform utilizes end-to-end encryption, ensuring it does not store any activity records. Like other email clients on the dark web, it does not require you to give your personal information. It is a Swiss-based company (privacy-friendly country), and all its tools are open-source, meaning anyone can test its vulnerabilities. SecureDrop is a secure hub for journalists and whistleblowers to interact and trade vital information.
Dark Web Links For News
Borderless news reporting and uncensored media are among the most important and practical uses for the dark web. Bypassing firewalls and other forms of geo-blocking helps people to access news websites and social media they normally wouldn’t be able to — and do so with less fear of recrimination. Reddit is actually available on the dark web now, so there’s no need to rely on third-party tools to access it via Tor. Just bear in mind that the addition of anonymity to a platform like Reddit causes people to behave without a filter. This onion site was created as a place for whistleblowers to pass information to journalists. It is a safe haven where anybody with information can share it anonymously and without fear of being tracked.
- The only difference is that it passes your traffic through random nodes before reaching the destination.
- Onion sites are part of the dark web, a hidden portion of the internet accessible only through specific software like the Tor Browser.
- I2P, though less popular, offers similar peer-to-peer anonymity with a focus on internal network services.
- The system is designed to provide enhanced security and privacy features.
News And Journalism

To appreciate why some users turn to the Hidden Wiki rather than Google, it’s important to understand the distinction between the surface web and the deep web. The surface web consists of all websites indexed by traditional search engines like Google, Bing, or Yahoo. This includes sites with publicly accessible content, such as news portals, blogs, and social media platforms. In contrast, the deep web encompasses parts of the internet not indexed by standard search engines. The dark web is a small part of the much larger “deep web,” which also isn’t indexed by search engines — but authorized users can access it using common web browsers.
Use Encrypted Communication Apps
Yes, you can still be tracked on the dark web despite its privacy features. Tracking can happen through IP leaks, browser vulnerabilities, or malicious exit nodes. To reduce this risk, use the Tor Browser properly, keep your software updated, avoid sharing personal information, and pair it with a reliable VPN. Following best practices for online anonymity helps, but staying cautious is essential since no method is completely foolproof. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it.
I found their technical explanations clear and well-researched, though the site updates less frequently than other news platforms. Secure communication for journalists, accessing privacy-focused forums, and whistleblower submissions. Onion links are URLs that end with .onion and can only be accessed through the Tor network.
What Is The Deepest Search Engine?
The Tor network is designed to provide you with privacy and anonymity. That said, most experts agree that at least some nodes on the Tor network have been compromised by intelligence agencies like the CIA and the NSA. What you may not know is that you can use Tor browser to access regular HTTPS websites on the surface web. This prevents tracking and fingerprinting, because Tor browser isolates each website you visit, meaning that third-party trackers and ad networks can’t follow you around. As the name suggests, Impreza Hosting is a (dark) web hosting service that provides all sorts of goodies such as domain names, host email services, and even servers for rent. So, you took my course on how to get on the dark web and want to explore your newfound superpower? mark it means it has been verified as a scam service and it should be avoided. This means that using the dark web may attract attention from your ISP or even law enforcement.|Downloading tainted files or clicking suspicious links can install malware on your device, so be cautious when surfing the web. As mentioned earlier, many websites consider Tor suspicious and block users entirely. Sometimes, you can access a website but won’t be able to login on your Tor browser. Likewise, some websites allow Tor, but with frequent Captchas that can be annoying. The performance of entry, middle, and exit nodes can vary, and some are slower than others.}
ONION SERVICES ERRORS
- Using a VPN is perhaps the easiest and most efficient way to protect your online travels from prying eyes, as it hides your real IP address, and encrypts all of your online traffic.
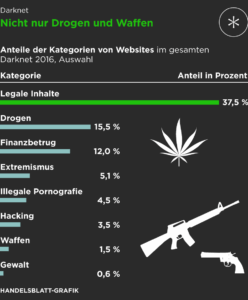
- One can also find drugs, crime services, stolen cards, and other illicit activities being offered by hackers.
- Scammers and criminals are lurking everywhere to take advantage of the unwary.
- The exit node – where your traffic leaves the Tor network and goes to its final destination – is another point of vulnerability.
- It emphasizes anonymity while providing familiar social media features.
Just as you explore hidden corners of the internet, you need to secure your data on the go. Easily initiate data encryption on your external drives and disks, ensuring compliance with your specific company policies. Encryption-2-Go offers controlled encryption, container-based or directory encryption, and even detects existing BitLocker To Go encrypted drives. With configurable user selection dialogs, it provides a user-friendly experience while maintaining strict security. As you discover the hidden depths of the web, ensure your sensitive data remains protected, no matter where it travels. Tor was designed specifically to provide anonymity on the internet, and Tor Onion Services address one of the Tor network’s biggest weaknesses (Tor exit nodes).
Search The Web
Onion sites do not use regular domain names that are registered with a central authority (domain name registry). Instead, onion sites are derived from a cryptographic key and must be accessed using the Tor browser. It serves the same purpose as ProPublica – facilitating access in countries where it may otherwise be restricted. Facebook’s onion portal is an essential communication tool for people living under oppressive regimes, despite the social media giant’s controversial reputation when it comes to privacy. Your ISP, and possibly the authorities, may decide to start monitoring your activity more closely to look for threats or illegal activity.

If you’re new to the deep/dark web, DuckDuckGo’s onion link should be your first port of call. This parent site gives access to all other dark websites through a simple search. Click its “Onionize” button to search the onion links for any other dark web websites. If you’re new to the dark web, start with the resources in our list. These trusted sites will help you gain confidence and minimize risks.

OnionLand Search
While some studies have claimed that illegal Bitcoin activity is as high as 44%. Simply accessing the dark web and using the Tor browser may already raise government suspicion. This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware. The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe.