The Tor Network provided a way to open safe communication channels for political dissidents, while also offering a channel for American intelligence operatives to communicate from around the globe. Journalists in overly restrictive countries also appreciate the anonymity of the dark web. Unlike the surface and deep web, you can’t access the dark web via a standard or specialized search engine. To access the dark web, you’ll need a specific set of tools – more about that later in the step-by-step section.
Use Active Monitoring Of Financial And Identity Theft
Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?). It also offers works of art, course material, and audiobooks for download. Wasabi Wallet is a Bitcoin wallet that not only hides all your data in the Tor network but also allows you to “join” your transactions with others to increase your anonymity. The dark web exists inside layered proxy networks, known as darknets. Tor, or “The Onion Router” is by far the largest of these darknets. The BBC’s international edition Tor version is available on the dark web, giving access to unbiased news in regions where the BBC is blocked or censored.
Beyond the sale of stolen data, the dark web facilitates the proliferation of cyber threats. Tools for hacking, malware, and ransomware are readily available for purchase, lowering the barrier for cybercriminals to launch sophisticated attacks. Forums on the dark web also provide spaces for malicious actors to exchange knowledge, collaborate, and refine their techniques. Kurt Baker is the senior director of product marketing for Falcon Intelligence at CrowdStrike. He has over 25 years of experience in senior leadership positions, specializing in emerging software companies.
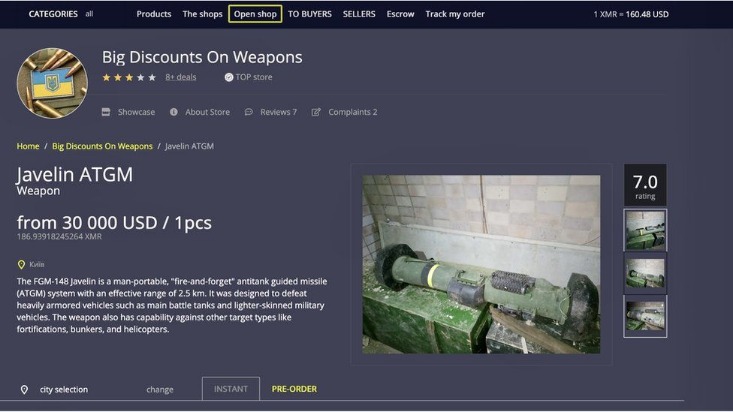
The surface web is the open part of the internet, which includes publicly accessible websites and resources. Search engines index all the web resources on the surface web, so you can search for them online. You just need standard browsers like Chrome, Edge, and Safari to open websites on the surface web. The dark web often connotes illicit activities like illegal drug sales and hacking. However, it also supports legitimate uses like protecting free speech and accessing information in censored regions. Legal uses include forums for free speech and privacy, while illegal activities may involve the sale of drugs, weapons, or stolen data.
Protecting Yourself On The Dark Web
Matt Egan is Global Content Director of Foundry, publisher of Tech Advisor, and a passionate technology fan who writes on subjects as diverse as smartphones, internet security, social media and Windows. Although all of these terms tend to be used interchangeably, they don’t refer to exactly the same thing. The Deep Web refers to all web pages that search engines cannot find. To visit a site on the Dark Web that is using Tor encryption, you have to use Tor. Just as your IP address is bounced through several layers of encryption to appear to be at another IP address on the Tor network, so is that of the website.

V Useful And Interesting Dark Web Resources

What’s more, they can also sell you personal information on the dark web as your personal data has a monetary value on the dark web. You can check our guide on the best VPN services to find the right VPN solution to protect your privacy. For example, your Geekflare.com—your trusted business resource for growth exists on the surface web. To reach Geekflare.com, you can either type its URL in your standard web browser or search for Geekflare in your favorite search engine.
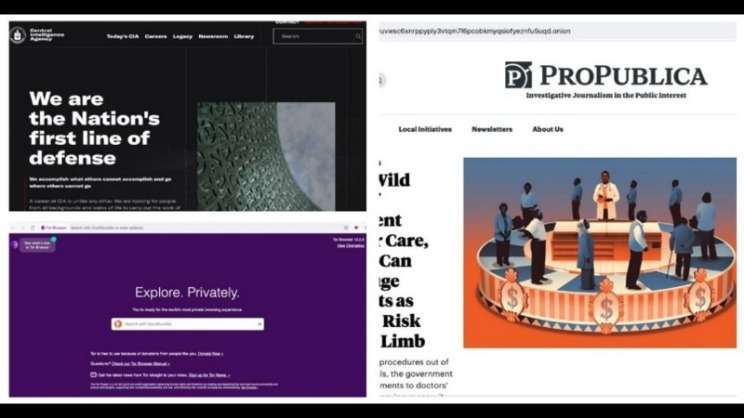
Media Outlets With A Secret Door
We’ll delve into the intriguing aspects of the dark web and guide you through some of its most notable sites. The dark web is home to the internet’s hidden sites, services, and products — some innocent, others downright dangerous. Read on to learn the pros and cons of the dark web, how to access it, and get tips for staying safe. Then, install Norton 360 Deluxe to get AI-powered scam detection to help secure your browsing against online threats. The dark web refers to web pages that are not indexed by commonly used search engines.
You won’t find any “hidden” stories here—it’s the same content as the normal web edition—but users in countries with government censorship will appreciate having a secure way to access it. However, many are used for illegal activity and onion websites are often popular hangouts for cybercriminals and scammers. Using common sense like avoiding clicking on shady links or download buttons, sticking to known sites and adding a VPN for an extra layer of protection, you should be fine. While accessing the dark web itself is not illegal in most countries, engaging with illicit activities or even visiting suspicious websites can attract the attention of law enforcement agencies.
Tor Links
Tor allows you to circumvent these restrictions and get access to worldwide news, such as the BBC website shown below. This guide will teach you how to install the Tor Browser in Windows easily so you can access the Dark Web or browse the web anonymously. The same general process applies to other operating systems, as Tor is also available for Mac and Linux. Install Avast SecureLine VPN for iOS to protect your privacy and keep your data from falling into the wrong hands. Install Avast SecureLine VPN for Android to protect your privacy and keep your data from falling into the wrong hands.
Perhaps some of them are traps laid by the authorities to catch people who try to hire assassins, buy weapons, or acquire counterfeit currency. There’s no such thing as perfectly private or secure on the internet. It’s still possible to track someone’s traffic pinging through the Tor nodes, though it is difficult.

How To Access The Dark Web Using The Tor Browser
The dark web isn’t just one sketchy marketplace hiding in a corner of the internet; it’s more like a messy, unregulated community with everything from freedom fighters to full-blown cybercriminals. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. Look no further if you want good music while navigating the dark web.
- Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web.
- Deep web sites may be concealed behind passwords or other security walls, while others simply tell search engines to not “crawl” them.
- This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware.
- Here are some of the now-defunct dark web markets that were notorious for cybercrime.
- Note that Hidden Wiki links sometimes lead to unsafe content, so be wary about what you click.
They’re built on top of the normal Internet, but they require special software to access, so they aren’t normally visible or accessible to people who aren’t in the know. If you have a legitimate or viable need to access the dark web, you’ll want to make sure you stay safe if you decide to use it. Some of these are well-known, established threats that circulate in this nook of the web.
What Is A Cloud Access Security Broker?
The most widely used tool for accessing the dark web is the Tor (The Onion Router) network, which uses a method called onion routing to obscure user identities and activities. The open web, also called the surface web, includes any public web content that is indexed by search engines. Webpages on the open web will show up in search results on sites like Google and Bing. Though a large volume of traffic visits on the open web every day, it only represents 4% of the content on the internet.
Always exercise extreme caution and verify the legality of any services you access. This isolates any potential malware and prevents cross-contamination with your personal data. Using Tails OS can further security, as all your data is reset every time you close the device. Alt Address provides disposable email addresses specifically designed for dark web use.



